(Downloads - 0)
For more info about our services contact : help@bestpfe.com
Table of contents
Chapter 1 General Introduction
1.1 Motivations
1.2 General Context
1.3 Access Control Issues and Requirements in Distributed Collaborative Editors
1.4 Undoability in Distributed Collaborative Editors
1.5 Contributions
1.6 Thesis organization
Chapter 2 State of the Art
2.1 Collaborative Editors
2.1.1 Real Time Collaborative Editors
2.1.2 Overview on the Operational Transformation (OT) Approach
2.2 Access Control for Collaborative Editors
2.2.1 Access Control Issues and Requirements in Collaborative Applications
2.2.2 Classes of Access Control Policies
2.2.3 Access Control in Database Area
2.2.4 Access Control for P2P Systems
2.2.5 Comparing Existing Solutions
2.3 Conclusion
Chapter 3 Our Generic Access Control Model
3.1 Coordination Model
3.1.1 Shared Data Object
3.1.2 Shared Policy Object
3.1.3 Single and Multi-Administrator Approaches
3.2 Concurrency and Security Issues
3.2.1 Out-of-order Execution of Cooperative and Administrative Operations
3.2.2 Joint Issue
3.2.3 Remote Check and Unnecessary Undo
3.3 A Generic Security Model
3.4 Distributed Garbage Collection for Administrative Logs
3.4.1 Garbage Collection Issues
3.5 Conclusion
Chapter 4 Concurrency Control Algorithms and Correctness Proof
4.1 Concurrency Control Algorithms
4.1.1 Cooperative Requests
4.1.2 Administrative Requests
4.1.3 Causality Between Cooperative and Administrative Requests
4.1.4 Control Procedures
4.1.5 Check Procedures
4.1.6 Administrative Procedures
4.1.7 Asymptotic Time Complexities
4.1.8 Illustrative Example
4.2 Correctness Proof
4.2.1 General Principles
4.2.2 The Correctness Criteria
4.3 Conclusion
Chapter 5 On the Undoability Problem in Distributed Collaborative Editors
5.1 Notations
5.2 Undo Approach
5.2.1 Principle
5.2.2 Undo Effect
5.2.3 Undo Properties
5.2.4 Illustrative Examples
5.3 Related Work
5.3.1 Proposed Undo Solutions for Single-user Editors
5.3.2 Undo Solutions for Collaborative Editors
5.4 Conclusion
Chapter 6 A Necessary and Sufficient Condition for Undoability
6.1 Formal Problem Statement
6.2 Necessary and Sufficient Condition for Undoability
6.2.1 CCO Properties
6.2.2 CSP Model
6.2.3 Necessary and Sufficient Condition for Undoability
6.2.4 Discussion
6.3 Our Generic Undo Framework
6.3.1 The Hide Relation
6.3.2 Transformation Rules
6.3.3 Illustrative Example
6.3.4 Asymptotic Time Complexity of the Undo Command
6.4 Conclusion
Chapter 7 Experimental Study and Performance Measurements
7.1 Coordination Framework
7.1.1 OPTIC Characteristics
7.1.2 Garbage Collector for Cooperative Logs
7.2 Developement Frameworks
7.2.1 JXTA
7.2.2 NetBeans
7.2.3 Grid’5000
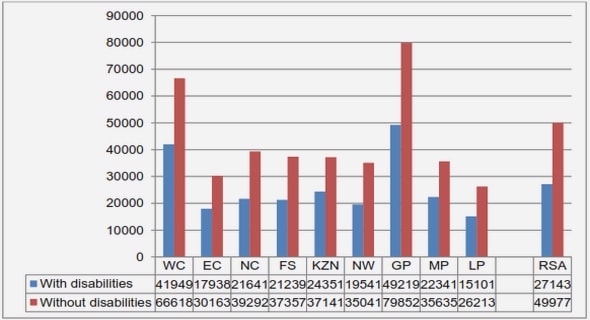
7.3 Experimental Results for the Coordination Layer
7.3.1 Metrics
7.3.2 Performances of the Desktop Application
7.3.3 Performances of the Mobile Devices Application
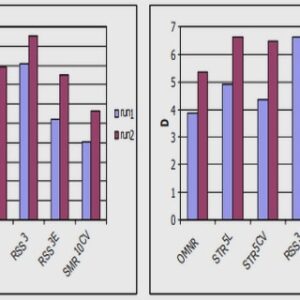
7.4 Experimental Results for the Security Layer
7.4.1 P2PAgenda Prototype
7.4.2 Processing Time for Checking Local and Remote Requests
7.4.3 Response Time Variation with Peers Number
7.4.4 Access Control Overhead
7.5 Conclusion
Chapter 8 General Conclusion
8.1 Summary
8.1.1 Why RCE Require Access Control?
8.1.2 Access Control Requirements and Issues
8.1.3 Undoing Operations in RCE
8.2 Summary of the Contributions
8.3 Directions for Future Work
Appendix A Correctness Proof of the Undo Approach
A.1 Hide Relation Properties
A.2 Inverse properties Preservation
A.3 Transformation Properties Preservation
A.3.1 TP1 Preservation
A.3.2 TP2 Preservation
Appendix B
A Distributed Garbage Collector for Cooperative Logs
B.1 The Coordination Framework OPTIC
B.2 Garbage Collection Issues
B.3 Garbage Collection Algorithm
B.4 Illustrative Examples
Bibliography