Get Complete Project Material File(s) Now!
Background
Energy-awareness is a well-studied problem, with a rich history stretching back to the advent of the first few computer wireless networks . However due to the unique design requirements in WSNs virtually every aspect of the system’s design can be considered for energy saving techniques [6]. In this chapter we however, limit the scope of our background literature search on select work based on energy saving mechanisms at the data link-layer. We go over the available methods and point out their unique functionalities explaining various proposed schemes in the literature. We also try to qualitatively compare the various available methods towards the end of the chapter.
Protocol Design Issues
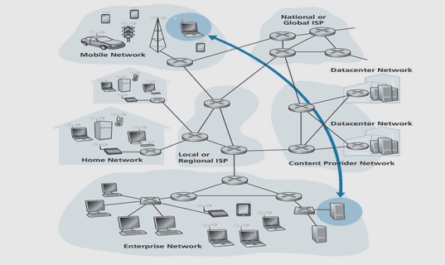
WSNs are generally deployed in resource-constrained environments where the longevity and sustenance of the WSN is dependent on the co-operation of all the nodes in the neighborhood as well as the different layers in the protocol stack (shown in Figure 2.1) of each of the sensor nodes. The protocol stack consists of the application layer, transport layer, network layer, data link layer, and physical layer. In conjunction with the various layers in WSNs the sensor nodes use power management to use available power. Scheduling the sensing tasks to specific nodes within the site of occurrence is managed by Task management. Factors that influence task management include the status of varying power levels of nodes in the WSN so that not all sensor nodes in a given region are required to sense. Mobility management is required to detect and register the movement of sensor nodes so that information of neighboring nodes is kept up-to-date. Networking within the umpteen sensor nodes is possible due to these management features incorporated within the WSN protocol stack that allow sensor nodes to work collaboratively, route data efficiently, and share the limited resources most optimally. Based on the sensing application that the WSN is being deployed for, application software can be built and used for the application layer. Based on the requirement of the sensing application/task the transport layer provides a reliable flow of data from transmitting node to receiving node. The network layer is concerned with the routing of data from the transport layer and the data link layer addresses methods on achieving a reliable, efficient communication between two communicating nodes. Factors such as propagation delay, energy awareness, medium access and error control are managed within the data link layer. Finally the physical layer addresses issues responsible for frequency selection, signal detection, modulation and encryption. While most of the above-mentioned entities would need to be handled rather seriously in existing networks, WSNs do not need to address all the attributes for their successful use. As traditional networks may aim to achieve high quality of service (QoS) provisions, sensor network protocols must focus primarily on power conservation due to limited, generally irreplaceable, power sources that can decide the longevity of the deployed WSN. Among the protocol layers discussed above the link-layer entities must specifically sense the environment and signal it to the upper layer entities for appropriate adaptation to adjust for link availability, link capacity, latency, congestion status and existing error conditions. A few issues discussed here explain the importance of the need to design a robust datalink layer. When there is no event, the entire system including the data link layer should hibernate. The data link layer should use distributed methods so that clear and frequent communication across sites, achieving coordinated and standardized measures becomes possible. Furthermore, a distributed network is more scalable and more robust because it has no infrastructure. Global synchronization must not be required in the data link layer. Since large numbers of sensor nodes are deployed densely in a WSN, neighboring nodes stay very close to one another making short distance one hop communication a clear choice so that lesser power can be consumed. The limited bandwidth of wireless channels between nodes, low-power consumption requirements further aggravates the situation, as message overheads need to be kept at a minimum level over the single-hop communications. They must have inbuilt tradeoff mechanisms that give the end user the option of prolonging network lifetime at the cost of lower throughput or higher transmission delay. Power is consumed only if a “data-centric” event occurs. Finally, the data link layer design needs to be simple and robust.
Motivation
The Medium Access Control (MAC) supported in the data link layer is an essential functionality that can be exploited for increased energy saving. The MAC in general is responsible for placing data on the transmission media, deciding when to listen and when to talk, and handling fixed-length parts of packets in the network. The MAC is also responsible for sharing the limited communication resources fairly and efficiently between the nodes. MAC in sensor networks however needs to be very different from the traditional networks because of its constraints on computational ability, storage and energy resources. Therefore medium access control should be energy efficient and should help with a fair utilization of the bandwidth among all the nodes in the network. In sensor networks, the primary objective is to sample the residing environment for information and send it to a higher processing infrastructure (base station) after processing it. The data traffic may be low for lengthy periods with intense traffic in between for short periods of time . Most of the time, the traffic is multihop and heading towards some larger processing infrastructure. At each of the nodes, there is traffic originating out of the node and traffic being routed through the node – because most nodes act as both data sources and routers. There are several restrictions on sensor nodes too. They can have little or no dedicated carrier sensing (CS) or collision detection (CD) embedded as a part of their hardware (unlike the case in traditional network hardware where additional circuitry is used for CS/CD [30]). Based on application specific they usually have no specific protocol stacks, which could specify the design of their media access protocol.
Sensor MAC Protocol Requirements
There have been many proposed MAC protocols in the literature specific to ad-hoc wireless networks. The proposed MAC channel access methods in ad hoc networks can be broadly divided into two categories: contention based and organized methods as outlined in [1]. Even though modifications have been suggested to the proposed ad hoc protocols with reference to WSNs, they are all not well suited for WSNs because of unique functionalities. To illustrate the reason a few differences are outlined here
WSNs have very limited power, and processing capability in comparison to adhoc networks.
The numbers of nodes in the WSN outnumber the nodes in ad-hoc networks by very large numbers.
In WSNs the frequent changes in the topology due to the nature of operation of nodes gives rise to a dynamic topology.
WSNs mostly use a broadcast communication model as compared to the point-to point communication paradigm used in ad-hoc networks.
The requirements of the sensor network MAC protocol design that differ from the MAC protocol of conventional wireless networks are as follows:
Power efficiency: Radio is one of the most energy consuming parts in a sensor node. The primary sources of energy waste in the radio of a sensor node are collisions, idle listening, overhearing and control packets. Collision causes a packet to be corrupted by another packet. Since this packet is discarded, the energy consumption per successful transmission will increase. Idle listening occurs when the node consumes power listening to the channel for possible traffic even when there is no packet to be received on the channel. Overhearing occurs when a node consumes energy to receive a packet that is not destined to it. Finally, the number of control packets should be minimized to eliminate the energy consumption related to them. Real-time deadline: Many applications require the guaranteed arrival of sensor data to Access Point (AP) within a specific deadline. One example is security monitoring. Another example may be traffic light controller. In traffic light controller, sensor nodes are placed along the road near the traffic light and inform the AP of the number of cars waiting behind the lights along each direction. AP then adjusts the duration of the lights accordingly. Since the traffic light duration is around 30-90 seconds, MAC protocol should be able to guarantee an upper bound on the maximum delay from the sampling of the sensors until the time when data reaches AP. Congestion control: Congestion control schemes adjust the traffic generation rate based on the feedback from the network. This is necessary in sensor networks so as to eliminate the bottleneck at the sensor nodes near AP since the traffic generated at all nodes pass through a few nodes around AP. The control scheme affects both the delay that each packet experiences and the power consumption per successful transmission. If the packet generation rate is above the rate that the network can handle, the queue length at the nodes on the route to AP increases, which causes an increase in the delay of the packets. Moreover, if the queue length of a node increases too much so that some packets are dropped, energy invested in these packets at each hop from their source to this node is wasted. Fairness: The aim of most of the sensor network applications is to collect the same amount of data from each node in the field. Receiving higher number of packets from one sensor node at the cost of lower number of packets received from the other one should be eliminated. Therefore, the scheme should maximize the minimum number of packets received from the nodes in the network.
Sensor MAC Protocol – Proposed Schemes
Now we discuss some of the well known MAC protocols in the realm of WSNs along with a discussion on a few specific protocols for ad-hoc networks that have inspired the existing design of protocols for WSNs. Current MAC protocols for sensor networks can be divided into contention-based and TDMA protocols. We start with the review of previously proposed contention-based protocols and then continue with TDMA-based protocols. The first class of protocols is contention based protocols. The MAC protocols in this class that provide power efficiency are based on exploiting the absence of traffic in listening state by putting the radio in sleep mode. These protocols differ from each other according to the radio wake-up algorithm. In [21], a separate wake-up radio is used to power down the normal data radio as long as there is no packet transmission or reception, based on the assumption that the listen mode of the wake-up radio is ultra low power. If a neighbor node wants to transmit a packet, it first sends a wake-up beacon over a wake-up channel to trigger the power up of the normal radio and then sends the data packet over the data radio. This protocol is successful in avoiding overhearing and idle listening problems in the data radio, but it is unable to solve the collision problem. Moreover, the difference in the transmission range between data and wake-up radio may pose significant problems.
CSMA Based Protocol
IEEE 802.11 Standard [47] is a multiple access technique based on CSMA/CA (Collision Sense Multiple Access/Collision Avoidance) [48]. While many improvements over the original 802.11 standard (Table 1 below) in terms of bandwidth, speed, modulation-schemes have been incorporated as part of wireless technologies as shown in Table 1 and standards [11], the basic protocol still remains the same. It lets the sender initially sense the carrier or medium to determine if it is idle for use by the sender. If the carrier is busy, the mobile defers transmission and enters the back-off state. The time period following this transmission is called the contention window and consists of a pre-determined number of transmission slots. The mobile, which entered back-off, randomly selects a slot in the contention window. It also continuously senses the medium during the time up to its selected contention slot. If it detects transmission from some other mobile during that period, it enters the back-off state again. If no transmission is detected, it transmits the access packet and captures the medium. The MACA protocol, addresses the hidden terminal and exposed node problem in 802.11. Extensions to the basic protocol include provisions for MAC-level acknowledgments and Request-To-Send (RTS)/Clear-To-Send (CTS) mechanisms. The IEEE 802.11 standard recommends the following technique for power conservation. A mobile that wishes to conserve energy may switch to sleep mode and inform the base station of this decision. From then on, the base station buffers packets received from the rest of the network that are destined for the sleeping mobile. The base station periodically transmits a beacon that contains information about such buffered packets. When the mobile wakes up, it listens for this beacon and responds to the base station which then forwards the packets. This approach conserves energy but results in additional delays at the mobile that may affect the quality of service (QoS). It is essential to quantify this delay in the presence of QoS delay bounds for individual connections. A comparison of energy-saving mechanisms in the IEEE 802.11 and HIPERLAN .
1. Introduction
1.1 Wireless Sensor Networks
1.2 Wireless Sensor Node
1.3 Meeting the Design Goals
1.4 Contributions of this research
1.5 Thesis Organization
2. Background
2.1 Protocol Design Issues
2.2 Motivation
2.3 Sensor MAC Protocol Requirements
2.4 Sensor MAC Protocol – Proposed Schemes
2.5 Qualitative comparison of Proposed MAC Schemes
3. Proposed Scheme
3.1 General Outline
3.2 Dynamic Cluster communications
3.3 Adaptive scheme for traffic adaptability
4. Design models and MAC description
4.1 Sensor Node design in ns-2
4.2 Incorporated MAC functionality
5. Discussion of Results
5.1 Metric Analyses
6. Conclusions and Future Work
6.1 Thesis Contributions
6.2 Future Work
GET THE COMPLETE PROJECT
An Energy Efficient Cross Layer Design Scheme for Wireless Sensor Networks