Get Complete Project Material File(s) Now! »
Social Technical System Theory
The social-technical system theory states that when an organizational system is designed, it is imperative to consider both the social and technical aspect in the complex system as they are interdependent on one another. The social-technical perspective originates from pioneering work since in the 1960s, at the Tavistock institute and has been continued on a worldwide basis (Mumford, 2006). The elements that are incorporated in this theory consists of first the people, who have a common objective to achieve a goal. Secondly, the technology, which they use to operate in a physical infrastructure, processes, and share values culture and norms (Malatji, M., Von Solms, S & Marnewick, A., 2019). For the theory to be effective, they must be interactions, and interdependencies in all the sub-systems.
The ecosystem of socio-technical system theory in figure 1 above, features the interdependencies of all the sub-systems, where there are integration and interactions within the organizational infrastructure. Relating the above theory to our study, some researchers have also incorporated the same theory in their research, in order to solve a common problem and understood how the socio-technical system could be deployed in an organization. Also, figure 2 below, shows the spherical structure of the socio-technical aspects and how they are embedded with each other but depicting different areas of operations.
Literature Review
Various studies by various researchers have explored the factors that affect information security risks management, and these are found various studies. This review will present studies that have sought to find out the influence of management support, technical experts support, funding and users’ security awareness on information security risks management.
Management Support
Management support is essential and important in implementing the factors of information security risk management because, it reflects in assigning IT Security managers in the company to identify the importance of security in their organizations. A successful implementation of information security risk management factors needs very qualified staff. The Management tends not to start any procedure to guarantee the security of organizations because naturally they feel that the IT department is responsible for selecting the correct technologies, installing the essential software tools, keeping the technology in the organization and to protect the organization’s information (Tryfonas, 2019). Therefore, the managements are in the position not only to identify business niches and opportunities but to make sufficient resources available for the implementation of ISM in the organization.
Alhogail, Mirza and Bakry (2015) worked on the comprehensive human factor framework for information security in organizations. The paper sought to bring together related human factors that have been identified in previous research into a logical, comprehensive framework. The framework was broken down into four diamond-shaped domains. Two domains are concerned with environmental and management issues, whereas the other two are concerned with preparedness and responsibility issues, representing an employee dimension. The domains at each of the diamond’s four corners interact with one another, influencing human behaviour in terms of information security. A survey of experts’ opinions on the framework was conducted to determine the importance of the framework’s various components in human behaviour. The framework served as a foundation for future research into information security in organizations, as well as the development of controls for this purpose.
In a similar study, Alhogail, and Mirza (2014) carried out a study on framework of information security culture change. This paper examined the various change management models that have been used in the field of information security. The framework then combined a set of change management principles proposed from previous studies into a comprehensive multistep framework that supports and guides the transition in information security culture change within organizations. Furthermore, these principles serve as the foundation for developing an appropriate guideline to aid in the effective implementation of information security culture change. Information security professionals and academic researchers can use the framework to help them take proactive steps and measures to help change the culture.
In addition, a study by Glushenko (2017) observed that information security management is process dependent, technology dependent and people dependent, but less attention have been considered for people involved in information security (Glushenko 2017). This is probably due to the tendency to view the problem from the approach of the organization’s requirement towards information security. Therefore, to handle these limitations, a questionnaire was constructed to gather information about factors influencing information security risk management from people directly and indirectly involved with organizational information structure. These factors were scrutinized and analysed with adjustable neuro-fuzzy inference system technique, machine learning method to reveal various critical factors affecting information security risk management. This approach revealed critical factors affecting the efficiency of managing the risks of information security as management support (Arogundade et al., 2021).
Arbanas and Hrustek (2019) investigated key success factors of information systems security. The study was based on a complete review of previous related study. The study therefore summarized the most frequently cited key success factors of information systems security identified in scientific articles indexed in relevant databases, with management support, information security policy, and information security education, training, and awareness ranking first, second, and third, respectively.
In the same vein, Semlambo, Mkude, and Lubua (2021) explored the factors affecting the security of information systems. This study discussed common factors affecting the security of information systems for modern computer users, including organizations and individuals, using a literature synthesis approach. The study results identified human factor, Unreliable information security policy, work environment and demographic factors as factors affecting information security management. According to a study conducted by Alhogail, Mirza, & Bakry (2015), human’s factor represents employees, management, and user and how they behave physically and psychological in relation to organizations IS security. Regarding unreliability of security policies, the study stated that information security policy can be defined as roles and responsibilities of employees to protect information system and technological resources of their organizations. These policies are implemented to help employees to properly manage technological resources and managers of the organizations should help employee to follow these policies. Mostly, organizations adopt/creates IS security policies for the sake of compliance to international standards or governments, hence these policies fail to provide reliable security as they only remain in documents and not being practice. The management fails to enforce policies to users and provide them with appropriate knowledge and regular training to equip them with reliable tools and knowledge about organizations IS security. As a result, assisting in the saving of time and money by concentrating limited resources on elements that cause real concern in IS security (Semlambo, Mkude, and Lubua, 2021).
A study conducted by Obeidat and Mughaid (2019) identified several risks and threats exist in the operational environment of computers and networks that stems from inadequate management control, particularly where they can become exposed to security breaches. The study observed that there could be various reasons for the vulnerabilities, starting with an incorrect installation of systems and inaccurate usage or malicious software. Because of the quantity of personnel, packages and structures increase in the organizations, the control of the groups’ information becomes more difficult and therefore vulnerability potential propagates. Considering preferable practice of hardware and software program, notwithstanding, encouraging, and empowering worker conduct, the organizations must make utilization of records and protection regulations through information security risks assessments (Obeidat and Mughaid, 2019).
Further findings of this study by Obeidat and Mughaid (2019) reported that one of the interviewees indicated that they are not allowed to do anything without permission from the management: the management need to give the employees support in implementing the security factors. Another expert said if the management does not understand the need to information security, then any attempt to prevent attacks and keep information safe will fail. Hone and Eloff (2017) clarified that the performance and the behaviour of employees towards information security becomes more coherent with secure behaviour if the top management shows concern about the organization information security. Thus, it is recommended that the security procedures are set by the attitudes of those at the topmost of the organization (Hinde, 2017).
Technical Experts Support
Yeo and Rahim (2016) states that the risk assessment team must have the expertise to apply the risk assessment methodology. Technical experts implement the risk assessment process based on the evaluation and understanding of existing systems designs and vulnerabilities associated with the potential benefits, costs and key performance indicator that realigned with new controls. According to Torres et al. (2006 as cited by Yeo and Rahim 2016), a critical success factor for ensuring security management of information systems is having honest, competent, smart, and skilful systems administrators.
A study conducted by Wangen and Snekkenes (2013) indicated that the primary goal of Information Security (IS) is to protect the business from threats and ensure daily operational success by ensuring confidentiality, integrity, availability, and non-repudiation. The author further stated that Information Security (IS) best practices rely heavily on well-functioning risk management (RM) processes, and RM is frequently regarded as the cornerstone of IS. Many public organizations rely on Information Security Risks management for them to be able to function optimally as information security management when it comes to organization, is made up of multifaceted processes which are influenced by a variety of factors such as the technical expert support through education, training, and technology, all of which must be managed within a single framework. According to Lundgren and Möller (2019), data confidentiality, integrity, and availability are the primary goals of information security.
Funding
All expert interviewees in a study conducted by Obeidat and Mughaid (2019), agreed that the budget is the major concern that affects the successful implementation of information security assessment. The budget is needed to buy the software tools for identifying the vulnerabilities and recommended controls, therefore, funding must be sufficient because without enough money organizations cannot be secured. Hinde (2017) defines budget as the financial facility which firstly estimates the costs and secondly measures the access required to the resources to reach a successful implementation of information security. Budgeting is dependent on the individuals’ investments strategy that yields outcomes, but the impact of security investment depends not only on the investor’s own decisions but also on the decisions of other variables (Canavan, 2018). One of the experts in the study conducted by Obeidat and Mughaid (2019), indicated that the vendors of security tools do not mention that after a while these tools must be updated to meet the new threats and attacks so without sufficient money the system organization becomes vulnerable to new attacks. It was, therefore, suggested that if organizations do not have the appropriate software or hardware tools, it would lead to difficulties in controlling some security concerns like access control tools, assisting employees to apply some security principles such as changing the password regularly or logging off after finishing their work. Another interviewee suggested that if they do not have the proper resources for implementing security measures, the goal of information security may not be feasibly clear to achieve within the organization.
A study conducted by Arogundade et al., (2021) on critical factors affecting the efficiency of information security risk management in business organization established that some of the known vital factors affecting the information security risk management are cost, organizational structure, organizational size, and philosophy of organization security which are all anchored on the funding. Organizational business practices have complementary support through information security risk management framework. Several organizations focus their attention of information security risk management efforts on the system of evaluation. Information security risk assessments (ISRAs) give organizations the ability of identifying crucial information assets and security risks (Werlinger et al. 2009).
Zhi, Atif and Maynard (2018) did a study on the factors that influence security investments in SMES. The study observed that information security risk management is a staged approach by which organizations can achieve a desired level of security. A risk assessment is aimed at identifying information assets that lies within the purview of an organization. Subsequently, threats and vulnerabilities are disclosed to develop scenarios that result in a breach of confidentiality, integrity, and availability.
Qualitative and quantitative methodologies were employed to estimate the probability of each scenario occurring and its associated impact (Gerber and Von Solm 2005 as cited by Zhi, Atif and Maynard, 2018). Subsequently, steps are taken for ensuring that information assets are protected to the greatest extent possible or to an acceptable level. The prioritized list of scenarios authorizes security expenditure to be directed towards the highest risks (that is, the scenarios with a moderately high impact and high probability). Organizations may control the risk by enforcing controls to prevent the potential breach from occurring (risk avoidance), reducing the impact after the breach has taken place (risk mitigation), doing nothing at all (risk acceptance) or placing the responsibility on an external party such as obtaining insurance (risk transfer) (Whitman and Mattord 2011 as cited by Zhi, Atif and Maynard, 2018).
Gerber and von Solms (2005) as cited by Zhi, Atif and Maynard, (2018) posited that lack of or inadequate risk assessment shows that the organization has not utilized its resources to the fullest in addressing security risk and vulnerability exposures. For example, should certain assets be not considered and reviewed in the risk assessment, then they may be unprotected. In the same way, if the estimation of probability and impact is inaccurate, not enough consideration has been given to security controls and protective strategy. Ultimately, vulnerability to information security risks can lead to adverse consequences for organizations, such as leakage of sensitive information and interruption or destruction of critical IT services. In the long run, the aim of risk management is to reduce the information security risk to an acceptable level in the organization (Gerber and von Solms 2005 as cited by Zhi, Atif and Maynard, 2018). Continuous performance of risk assessment in an organization allows for the application of systematic methods to identify security risks and guide them on the countermeasures and to defend their expenditure for security (Spinellis et al. 1999 as cited by Zhi, Atif and Maynard, 2018).
Users’ Security Awareness
Regarding the users’ security awareness, Dhillon (2017), posits that security of critical information can be accomplished through security awareness and training. However, expanding the awareness can be implemented through training of employees to establish a sense of information security within the organization (Dhillon, 2017). According to Dhillon (2017), organizations need to have continuing education and training plans to accomplish the essential outcome from the implementation of information security policies. The 2002 security awareness index report mentioned by ISO/IEC (2016) concluded that organizations all over the world are failing to make their employees aware of the security problems and concerns.
The human factor contributes mostly to the security incidents in every organization this assertion was supported the finding of Doherty and Fulford (2016) that employees are the biggest threat to information security. A use case of attacks through human factor is when employees themselves opened spam email or attached files. Majority of security exploitation comes from human error of omission, negligence, or intentional act. Therefore, human aspect needs to be seriously considered when it comes to information security. It is easily exploited and constantly overlooked. Companies spend millions of dollars on hardware, software, and security protection tools- firewalls, encryption mechanism, and secure access devices. It is almost money wasted because none of these measures address the weakest link in the security chain, where humans are the weakest link in the security chain. Therefore, if the security fails, that will weaken any organization (Anderson and Moore, 2018).
Some employees leave their computers on, other employees write the username and password on a small sheet near the computer, and this breaks the confidentiality to unauthorized people. That is why the research recommended doing a continuous course in training and awareness at all levels of the organization (Anderson and Moore, 2018).
Another study in the same vein conducted by Parsons, et al., (2010) observed that in every organization, employees are the greatest assets. However, the study posited that a well-trained employee brings about efficiency in the information security system. Therefore, training programs are the basic rudiments for information system security development process. When employees are trained properly in information security training programs, it helps to increase security awareness and productivity, which in overall leads to reduced cost of security. Greater participation in information security training programs is highly encouraged in all organization (Parsons, et al., 2010). The study recommended that information security training program should include regular evaluation and implementation of information technology based on the trends and changes. New challenges should be treated with the new technology. Therefore, the training awareness programs must be flexible to meet the new demand of the challenges. For this reason, IT experts should always attempt to develop themselves by attending various IT security awareness program to update themselves of the current issues in IT security measures. So, information security training programs are hereby considered in validating the model, and this hypothesis is proposed. Hypothesis 3 implies that there is a potential relationship between information security training programs and information security risk management (Parsons, et al., 2010).
Another study by Al-Omari, El-Gayar, and Deokar (2012) focused on user compliance with ICT policies to examine factors that affect IS security. The goal of the study was to produce a measurement tool that offers better measures for predicting and describing employees’ compliance with information security policies (ISPs) by exploring the role of information security awareness in improving employees’ compliance with ISPs. The study was the first to look at compliance intention from the viewpoint of users. In General, the investigation results show strong support for the proposed instrument and provide early confirmation of the validity of the underlying theoretical model.
The Concept of Information Security Risk Management
In the thought of Thorwat (2018), and Arbanas and Hrustek (2019), when the security of an organization’s information systems is breached, such an organization faces risks such as data loss, cyber security attacks and business loss. Sahar, Al-Sarti and Abdul (2017) observed that Information Security Management Systems provide requirements for establishing, implementing, maintaining, and improving an information security management system. This adoption is a strategic decision for an organization that is influenced by the organization’s needs and objectives, security requirements, and scaled based on the organization’s needs. The information security management system entails applying a risk management process to protect the confidentiality, integrity, and availability of information. The components of an information security management system include Risk management based upon metrics of confidentiality, integrity, and availability; total quality management (TQM) applied based upon metrics of efficiency and effectiveness, a monitoring and reporting model based upon abstraction layers; a structured approach that contains people, process, and technology and finally an extensible framework from which to manage information security compliance (Sahar, Al- Sarti and Abdul, 2017).
According to Kuzminykh et al., (2021), information security risk management is a process that consists of identification, management and elimination or reduction of the likelihood of events that can negatively affect the assets of the information system, for the purpose of risk reduction that can potentially have the possibility to affect the information system (Kuzminykh et al., (2021). In the opinion of Peitier (2017), information security risk assessment consists of four distinct stages: asset identification, threat identification, vulnerability identification, and control identification and implementation. Information security risk assessment is an important part of organizational risk management practices that helps the organisation to identify, assess, and prioritize risks against criteria for risk acceptance and objectives relevant to the organization (Kuzminykh et al., (2021). Peitier (2017) identifies some factors that affect information security risk assessment such as management support; users’ security awareness; technical experts and funding.
The ultimate target of information security policy is to provide confidentiality, availability, and integrity of information within any organization to eliminate cyber risks. The Institute of Risk Management (2018) defines cyber risk as any risk of financial loss, disruption, or damage to the reputation of an organization from a failure of its information technology systems. The possibility that an isolated cyber-attack could have consequences for the entire financial system is referred to as systemic risk (World Economic Forum, 2016). Every organization like the banking industry have their organizational aim, objectives, vision, and mission to make profit from their business. However, Nigerian commercial banks have been faced with cybersecurity challenges of how to secure its information from fraudsters, criminals, spamming as well as hackers to the information assets. For instance, according to Deloitte Nigeria, financial institutions, corporate businesses, state agencies and private individuals are increasingly being exposed to cyber-attacks and fraud through disinformation, impersonation, and other mechanisms such as phishing, which enables cybercriminals to access computers, mobile devices, and the intranet unnoticed to perform cyber- attacks from the inside (Ogbonnaya, 2020).
Information Security Risk Management Process
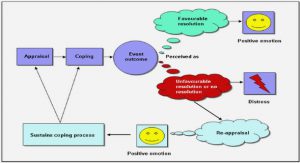
The above is the proposed information security risk management process in a nutshell. As the diagram in figure 3 stands, it sends a signal that before risk can be managed, it is very vital to be identified. As soon as the risk is identified, actions are taken to measure the intensity of the risk or to evaluate the result of the outcome.
Analysis/assessment process comes in to determine the consequences if any. Implementation of control measures are taken to avoid, reduce or transfer the risk depending on the magnitude or intensity. Thereafter, a monitoring steps are taken ascertain whether the expected process has been achieved (Bergström, Lundgren, & Ericson, 2019).
Before information risk management can be implemented, it must be identified first, because if there is no risk, there is nothing to measure, and nothing to value.
In the case of Nigerian commercial banks, cybersecurity risks need to be identified according to the threats and vulnerabilities the bank faces in their daily operations.
Cybersecurity Challenges (Risks) facing Nigerian Commercial Banks.
Information security risk can be analysed qualitatively in the case Nigerian commercial banks by considering the following cybersecurity challenges facing Nigerian commercial banks:
Ransomware: This type of attack happens when cybercriminals infect the system with a malicious file, that encrypts files/hard drive whereby users are logged out of their system, and eventually the criminals will start demanding a ransom (money), and in most cases, bitcoin from the innocent users before access to the files are given back to them (Wang, Nnaji, & Jung, (2020).
Social Engineering: Social engineering is one of the most powerful weapons used by cybercriminals on employees working in an organization. The reason is that people are the weakest and most vulnerable link in the chain of information security. Ugbe, (2021), stated that due to a lack of security awareness, people can be deceived in leaking some sensitive and critical information of their customers unknowingly. When it happens, it affects the bank employees and their customers, and even damage the reputation of the bank. Social engineering type of attacks can be in form of phishing, whaling, whereby emails with attachments claiming to be legitimate could be sent to massive receipts, but not knowing that it is a bait. It is imperative for all employees to be well informed about the security posture of the organization (Gaillard, A. 2021). Adequate provision of funds should be made available by the management to continuously train their staff as a going concern.
Need to secure cloud-base network: A lot of critical information and data of banks are being stored in the cloud infrastructure. Unfortunately, cybercriminal can still have access to compromise the data in the cloud. For this reason, it is important that banks should critically ensure that cloud infrastructure are well configured, do some configuration hardening to prevent any data breach. This is where the influence of the technical experts comes into play. Well qualified cybersecurity expert services are highly needed to configure and implement the paradigm of security. In a more favorable case scenario, partnering with a third-party security consultants or company will enhance the security posture (Pramanik, et al., 2022).
The risk of remote workers: As stated by Omodunbi, B. A., et al. (2020), due to the covid-19 pandemic there has been a paradigm shift from the normal work force to remote (home office) or hybrid work force are ubiquitous. This have also increased cybersecurity challenges in the banking sector. Some employees no longer access sensitive data through a secure network with secured encryption channels, and some uses their organization’s devices to access malicious website, thereby exposing the banks critical information to cybercriminal. For this reason, the influence of user’s security awareness training will play a crucial role to keep implementing continuous security awareness training for all employees.
Table of contents :
1 Introduction
1.1 Background of the Study
1.2 Statement of the Problem
1.3 Research Aim and Objectives
1.4 Research Scope and Delimitation
1.5 Justification for the Study
2 Theoretical Background
2.1 Theoretical Framework
2.1.1 Social Technical System Theory
2.2 Literature Review
2.2.1 Management Support
2.2.2 Technical Experts Support
2.2.3 Funding
2.2.4 Users’ Security Awareness
2.3 The Concept of Information Security Risk Management
2.4 Information Security Risk Management Process
2.5 Cybersecurity Challenges (Risks) facing Nigerian Commercial Banks.
2.6 Risk Assessment Measurement
2.7 Variables used to measure the above concepts
2.7.1 Dependent and Independent Variables
2.8 Factors Influencing the Implementation of ISRM in Nigerian Commercial Banks
2.8.1 User Information security Awareness and Training
2.8.2 Information Security Policy
2.8.3 Information Security Training Programs
2.8.4 Technical Experts’ Support
2.8.5 Motivation of Employees
2.8.6 Management Commitment and Support
2.8.7 Funding
2.9 Summary of the Theoretical Framework.
3 Research Methodology
3.1 Research Philosophy and Positivistic Paradigm.
3.2 Research Design
3.3 Population of the Study
3.4 Sampling Design
3.5 Data Collection Method
3.5.1 Qualitative Data
3.5.2 Quantitative Data
3.6 Research Model
3.7 Data Analysis and Presentation
3.8 Ethical Considerations
4 Result
4.1 Research Questionnaire Administration
4.2 Background Statistics and Demographics
4.2.1 Respondents Percentage Distribution of Staff Cadre
4.2.2 Percentage Distribution of Departmental Staff
4.2.3 Percentage Distribution of Working Experience
4.2.4 Percentage Distribution of Gender
4.2.5 Percentage Level of Education
4.3 Relationship between the Independent Variables and Dependent Variable
4.4 Joint Contributions of the Variables on ISRM
4.5 Relative Contribution of the Variables
5 Analysis and Discussions
5.1 Qualitative Interview Transcript
5.2 Descriptive Statistics Analysis of the Variables
5.3 Multiple Collinearity
5.4 Regression Analysis
5.5 Survey Data, 2022
5.6 Source: Research Data, 2022
5.7 Multiple Regression Analysis
5.8 Logistic Regression Summarization
6 Summary, Conclusion, and Recommendation
6.1 Summary
6.2 Conclusion
6.3 Recommendations
6.4 Limitations of the Study
6.5 Suggestions for Further Studies
REFERENCES: