Get Complete Project Material File(s) Now! »
Next-Generation Wireless Networks
The main driver of the evolution of wireless systems in the past was the need for higher data rates. However, with the proliferation of novel IoT applications, the key requirements that fifth generation (5G) and beyond cellular networks must guarantee are becoming more and more diverse. In fact, future communication networks have to support enhanced mobile broadband (eMBB) services, massive machine-type communications (mMTC) [44], and ultra-reliable low-latency communications (URLLC) [5, 6]. In particular, the main 5G key elements, illustrated in Fig. 2.1, can be summarized as:
• Higher data rates and better coverage: with an area capacity 1000 times higher than that provided by fourth generation (4G) mobile networks, and edge capacity exceeding that provided by 4G by 100 times.
• High reliability: with a packet error rate (PER) typically lower than 10−5.
• Low latency: with a round-trip air latency of 1 ms for some latency-constrained applications.
• Support for machine type devices: for example autonomous vehicles, UAVs, virtual reality headsets, connected sensors.
• Low energy consumption: communications for energy-constrained IoT devices (e.g., sensors) must be designed in a way to extend their lifetime. Moreover, for green communications, future communication systems must be able to increase system capacity while maintaining a low energy consumption at the base stations (BSs) level. To achieve these requirements, significant research efforts have been dedicated to the study of novel techniques and cellular network architectures that can cope with the rapid evolution of wireless systems. Among these, we cite:
• Dense deployment of distributed antenna systems (DASs) and small base stations (SBSs): Future communication networks will be characterized by a dense deployment of DASs and SBSs which will improve the area capacity and coverage, and decrease the system power consumption.
• Use of UAVs as flying BSs: The use of UAVs in cellular networks has been recently given a lot of attention. The applications of UAVs as flying BSs in communication networks are diverse and include among others, increasing the capacity and coverage in temporary hotspot areas, restoring communications in public safety scenarios, providing coverage to remote areas and gathering data from IoT devices.
• More efficient use of the existing spectrum: Novel multiple access techniques such as NOMA can be utilized to increase spectrum efficiency, the achieved rates and the number of served users. Next, we give a general overview of NOMA, a novel multiple access technique to be used in future communication networks. This overview is followed by a discussion of IoT applications in future wireless communication networks. Finally, an overview of the useof UAVs in cellular networks is presented.
Non-Orthogonal Multiple Access
In this section, the basic principles of NOMA are introduced.
NOMA is based on the concept that multiple users can be simultaneously served on the same orthogonal resource block, whether the same resource block is a frequency band, a timeslot or an orthogonal spatial degree of freedom [45]. Multiple categories of NOMA have been considered in the literature, among which we cite:
• power-domain NOMA (PD-NOMA) [28, 29, 30],
• sparse code multiple access (SCMA) [31, 46, 47],
• pattern division multiple access (PDMA) [32],
• interleave division multiple access (IDMA) [33].
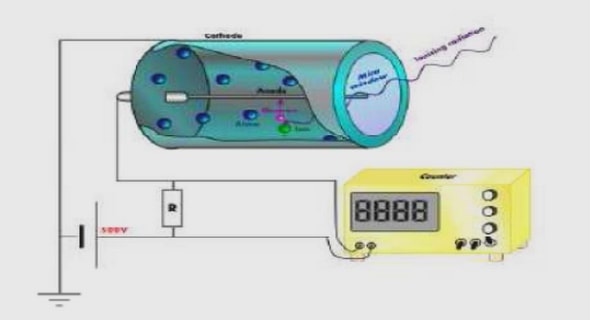
This thesis focuses on PD-NOMA, the concept of which will be discussed next. Note that for simplicity, PD-NOMA will be denoted by NOMA in this thesis. The basic concept of NOMA relies on exploiting the power domain to serve multiple users non-orthogonally on the same orthogonal frequency division multiplexing (OFDM) resource block. NOMA relies on superposition coding (SC) [7] at the transmitter side and on successive interference cancellation (SIC) [8] at the receiver side. Although the key components of NOMA, i.e., SC and SIC, have been invented more than two decades ago, the application of NOMA scheduling in wireless communication systems, i.e., removing the orthogonality between users, is relatively new. An illustration comparing NOMA and orthogonal multiple access (OMA) scheduling is shown in Fig. (2.2).
Basics of Uplink NOMA
In the uplink, the BS sends control signals to the transmitting users to determine power allocation. Once the transmit power is determined, each transmitting user sends its message. The BS in this case receives a signal constituted by the superposition of the signals of transmitting users. Using SIC, the BS decodes the messages of the users according to the decreasing order of channel gains. In other words, the signal of the user having the highest channel gain is first decoded, while considering the signals of all other users as interference. The signal of the user with the highest channel gain is then subtracted from the total received signal before decoding the signals of the remaining users. In uplink NOMA, the signal of the user with the lowest channel gain is decoded without interference. Considering the case of two scheduled users on subband s, ks(1) and ks(2) with ks(1) being the user with the higher channel gain, the achieved rates in uplink NOMA are given by.
Internet of Things and New Mobile Traffic Characteristics
Future wireless communication networks are expected to support billions of connected machine-type devices (MTDs) [9], giving rise to the IoT. These MTDs will be able to connect with each other and with the BSs over wireless links, allowing them to collect and exchange information in real-time. The applications considered for IoT devices are countless: smart grids, smart cities, smart homes, autonomous cars, health sensors, etc. These novel applications will help significantly enhance the quality of people’s lives. However, for efficient deployment of IoT services, many challenges such as data analytics, transmission capabilities, resource allocation, security and privacy, must be solved. In particular, the mobile traffic requirements of IoT devices are application-dependent. For example, the necessary traffic for efficient deployment of autonomous cars must benefit from a high reliability and a low latency, while normally requiring low data rates. On the other hand, applications like virtual or augmented reality require both high data rates and low latency.
Hence, the quality of service (QoS) requirements of IoT devices are very different from one another, and even more so from the QoS requirements of human users. To this effect, coming up with resource allocation techniques for IoT devices that can meet their diverse traffic requirements, in terms of throughput, latency and reliability, is of utmost importance.
UAV-Aided Communication Networks
Recently, the use of UAVs has received significant attention in various application domains spanning the military, surveillance and monitoring, delivery, and telecommunication domains, among others [42, 53, 54, 55]. Depending on the requirements of each application, different types of UAVs must be used. Based on their flying altitudes, UAVs can be partitioned into two categories: high altitude platforms (HAPs) and low altitude platforms (LAPs). HAPs are deployed on altitudes exceeding 17 km and are quasi-stationary. LAPs on their turn can occupy much lower altitudes, from 50 m and up to a few kilometers, have a flexible deployment and can move quickly. On the one hand, LAPs benefit from a rapid deployment, when compared to HAPs, making them suitable for time-sensitive applications. On the other hand, HAPs benefit from a longer battery life, making them suitable for long-term applications. UAVs can be also partitioned among rotary-wing and fixed-wing UAVs. Fixed-wing UAVs are heavier than rotary-wing UAVs, benefit from higher speeds, and must keep moving in order to stay aloft. On the contrary, rotary-wing UAVs can hover over a certain area if the application requires it.
In wireless communication systems, properly deployed and operated UAVs can provide solutions to many challenges. Indeed, UAVs can be deployed as aerial BSs to provide on-demand communications to areas in need. Thanks to their adjustable flying altitude, the probability of establishing line-of-sight (LOS) links between the UAV and its assigned users is increased, resulting in more efficient communications, when compared to ground BSs. Moreover, due to the flexible deployment of LAP UAVs, the capacity and coverage of UAV-enabled communication networks can be enhanced. Due to these numerous advantages, the use of UAVs as aerial BSs in wireless communication networks admits many potential applications. For example, UAVs can increase the capacity and coverage in temporary hotspot areas such as sport stadiums. UAVs can also restore communications in public safety scenarios to support search and rescue operations when terrestrial communication networks get damaged from natural disasters for example. UAVs can further aid in the IoT networks where devices normally have a low transmit power and are not able to communication over long ranges. In this case, UAVs can get close to IoT devices, allowing them to transmit their data efficiently.
Challenges of UAV Communications
To reap the benefits of UAVs in cellular communication systems, several challenges must be met. Among these challenges, we cite:
1. UAV-to-ground channel modeling: The first challenge relates to finding accurate models for the air-to-ground (A2G) channel between the UAV and the ground users. In fact, the A2G channel characteristics differ significantly from classical terrestrial channel models and any movement of the UAV can affect them. Furthermore, the A2G channel depends on the altitude of the UAV, its elevation angle and the propagation environment. Hence, finding generic and accurate channel models for UAV-to-ground communications is a challenging task.
2. Placement of the UAV: The optimal placement of the UAV in a wireless communication network depends on the objective of its deployment (e.g., coverage and capacity enhancement, power minimization of IoT communications). Naturally, the optimal placement of the UAV depends on the locations of the ground users and their traffic characteristics (e.g., latency, reliability and data rate requirements). Moreover, the deployment of a UAV should take into account managing inter-cell interference from other potentially deployed UAVs as well as from terrestrial BSs. In addition, the placement of the UAV must be optimized in 3D space and must account for the UAV energy constraints. Hence, the placement problem of a UAV-BS is much more challenging than that of a terrestrial BS.
3. Trajectory optimization: Optimizing the flight trajectory of the UAV is a challenging task as it necessitates accounting for the channel variation, the energy and the flight constraints.
Table of contents :
Contents
List of Figures
List of Tables
List of Abbreviations
1 Introduction
1.1 Motivations
1.1.1 Radio Access Techniques
1.1.2 Multiple Access Techniques
1.1.3 Distributed Antennas and Small Cell Deployment with Self Organizing Capabilities
1.1.4 UAV-Aided Communications
1.2 Thesis Contributions
1.3 List of Publications
1.3.1 Journal Publications
1.3.2 Conference Publications
1.4 Thesis Structure
2 Background
2.1 Next-Generation Wireless Networks
2.1.1 Non-Orthogonal Multiple Access
2.1.1.1 Basics of Downlink NOMA
2.1.1.2 Basics of Uplink NOMA
2.1.2 Internet of Things and New Mobile Traffic Characteristics .
2.1.3 UAV-Aided Communication Networks
2.1.3.1 Challenges of UAV Communications
2.1.3.2 Air-to-Ground Channel Modeling
2.2 Basics of Game Theory
2.3 Markov Chains and Related Concepts
2.3.1 Markov Chain: Definition
2.3.2 Classification of states
2.3.3 Classification of Chains
2.3.4 Adaptive Play
2.3.4.1 Adaptive Play When There Are No Mistakes
2.3.4.2 Adaptive Play With Mistakes
2.4 Multi-Armed Bandits
2.5 Matching Theory
2.6 Summary
3 Resource Allocation for Mixed Traffic
3.1 Introduction
3.1.1 Related Work
3.1.2 Problem Statement and Contributions
3.2 System Model and Problem Formulation
3.2.1 System Description
3.2.2 User Characteristics
3.2.2.1 BE Users
3.2.2.2 RT Users
3.2.3 Optimization Problem
3.3 Low-Complexity Greedy Algorithm
3.3.1 Phase 1: Assignment of Users and Subbands to Antennas
3.3.2 Phase 2: NOMA pairing on subbands assigned to RT users .
3.3.2.1 Scenario 1: hkRT ,s,as > hk0,s,as
3.3.2.2 Scenario 2: hkRT ,s,as < hk0,s,as
3.3.3 Global Resource Allocation Technique
3.3.4 Numerical Results
3.3.4.1 Evaluation of the Performance of RT Users
3.3.4.2 Evaluation of the Performance of BE Users
3.4 Matching Theory-Based Solution
3.4.1 Matching Theory-Based Solution in the OMA-CAS setting
3.4.1.1 Subband Allocation Problem as a Matching Game
3.4.1.2 Preference Lists
3.4.1.3 Proposed OMA-CAS DA Algorithm
3.4.2 Matching Theory-Based Solution in the OMA-DAS Context .
3.4.2.1 DAS Matching Game Model and Algorithm
3.4.2.2 Estimation of the number of subbands per antenna .
3.4.3 Matching Theory-Based Solution in the NOMA-CAS Context
3.4.3.1 Assignment of Subbands to Single RT Users and NOMA BE Users
3.4.3.2 NOMA Pairing on Subbands Assigned to RT Users
3.4.4 Matching Technique in the NOMA-DAS Context
3.4.5 Analysis of Stability, Convergence and Complexity
3.4.5.1 Properties of the Matching Technique
3.4.5.2 Properties of the Iterative Approach
3.4.6 Numerical Results
3.4.6.1 Convergence of the Proposed Method
3.4.6.2 Performance of the MM Technique
3.5 Summary
3.6 Appendix A
A.1 Proof of Theorem 3
A.2 Proof of Theorem 4
4 Uncoordinated Spectrum Access using Multi-Armed Bandits
4.1 Introduction
4.1.1 Related Work
4.1.2 Problem Statement and Contributions
4.2 System Model
4.2.1 Uncoordinated Channel Allocation
4.2.2 Distributed Power Allocation
4.3 Proposed Solution
4.3.1 Proposed Algorithm for the Channel Allocation Problem
4.3.2 Matching Dynamics
4.3.3 Proposed Solution for the Distributed Power Allocation
4.4 Regret Analysis
4.4.1 Regret in the Exploration Phase
4.4.2 Regret in the Matching Phase
4.4.3 Regret in the Exploitation Phase
4.4.4 Regret of the Proposed Technique
4.5 Exploration Phase
4.5.1 Estimation of the Reward Means
4.5.2 Estimating the number of APs
4.5.3 Length of the Channel Allocation Exploration Phase
4.6 Matching Phase
4.7 Uncoordinated Spectrum Access for Grant-Free Communications
4.8 Simulation Results
4.8.1 Performance of the OMA Version of the Uncoordinated Spectrum Access
4.8.2 Performance of the Uncoordinated Spectrum Access and Power Control in a SON
4.8.2.1 Estimation Accuracy of the Exploration Phase
4.8.2.2 Performance Analysis
4.9 Summary
4.10 Appendix A
A.1 Proof of Lemma 1
A.2 Proof of Lemma 2
A.2.1 Lower Bound of the Length of the Exploration Phase in the Channel Allocation Step
A.2.2 Lower Bound of the Length of the Exploration Phase in the Power Allocation Step
A.3 Proof of Lemma 3
A.4 Proof of Lemma 5
5 UAV-Enabled Communication Networks
5.1 Introduction
5.1.1 Background
5.1.2 Problem Statement and Contributions
5.2 System Model
5.2.1 Path Loss Model
5.2.2 Communication Model
5.2.3 Problem Formulation
5.3 Coverage Region of Each User and of the MBS
5.4 Holistic Solution to the Positioning and Resource Allocation Problems in UAV-Enabled Networks
5.4.1 Preliminaries
5.4.1.1 Subband Assignment in the Access Link
5.4.1.2 Feasibility Test
5.4.1.3 Initialization of the Access Power Values
5.4.1.4 MBS Coverage Radius
5.4.2 Proposed Solution
5.4.2.1 Finding the minimum number of required backhaul subbands
5.4.2.2 Deciding on the number and choice of backhaul subbands
5.4.2.3 Finding the optimal UAV position and the final power levels
5.4.3 NOMA Pairing to Account for the Case where the Rate Requirements Cannot Be Met with Pmax UAV
5.4.3.1 Finding the Maximum Achievable Rates with Pmax UAV
5.4.3.2 Finding the Candidate Subbands for NOMA Pairing .
5.4.3.3 Determining the Eligible Subbands for Each User
5.4.3.4 NOMA Pairing and Power Optimization
5.4.4 Summary of the Proposed Solution
5.5 Simplified Solution to the Positioning and Resource Allocation Problems in UAV-Enabled Networks
5.5.1 Preliminaries
5.5.2 Proposed Solution
5.5.2.1 Deciding on the Subband Assignment in the Backhaul Link
5.5.2.2 Finding the Optimal UAV Position and the Final Power Levels
5.6 Simulation Results
5.6.1 Compared Methods
5.6.2 Convergence of the Proposed Technique
5.6.3 Performance of the Proposed Technique
5.7 Summary
5.8 Appendix A
A.1 Proof of Proposition 4
A.2 Solution to Problem (5.60)
A.2.1 Subband n is not used in the backhaul link
A.2.2 Subband n is used in the backhaul link
6 Conclusions and Future Work
6.1 Summary
6.1.1 Resource Allocation for Mixed Traffic Systems
6.1.2 Uncoordinated Spectrum Access using Multi-Armed Bandits
6.1.3 UAV-Enabled Communication Networks
6.2 Future Work
Bibliography