Get Complete Project Material File(s) Now! »
RESEARCH PURPOSE, PROBLEMS AND GOALS
This chapter explains the project purpose, problem domain, project goals and the research question. Reader will be given an understanding of why SCADA cyber security is crucial and why the requirement of its improvement is felt.
Project Purpose
The objectives of this project are:
• To identify vulnerabilities and causes because of human negligence respective of installation, configuration, operation and management in SCADA system.
• Scale them with respect to the potential damage possibly caused by their vulnerability exploitations, and countermeasure suggestions against those vulnerabilities.
Problem Domain
Seeking technological improvements in SCADA system to prevent cyber attack is important. The processing, controlling, maintenance and configuration of such system depend on human initiated actions, so prevent users from making awful decisions is difficult. When the individuals involved in operation expose system to threats because of negligence, the collection of these makes it dangerous for entire project.
The System Administrators and/or operators may introduce vulnerabilities in system due to the inaccurate installation and configuration of antivirus, firewalls, IDS etc. Other cases of incorrect security implementations include failure to use auditing functions, examination of existing log files, granting unnecessary access rights, failure to review access rights at regular intervals, multiple assignment of the same log-in name, inappropriate process management, existence of unnecessary open ports and unused services, carelessness to monitor in/out traffic, analyze implementation of weak password policy [7] and failure to use the available security tools [11]. In case of poor configuration of the network components, the availability of entire network can disrupt, furthermore confidentiality and integrity of data can be impaired. For example an unnecessary program at system boot up could leave system open for cyber attack. Hence there is a need of careful configuration, maintenance and operation of installed systems
Goals
Human and organizational behavior plays key role in security of an organization.
Main goals of this thesis are
o Identifying unwanted behaviors that users and administrators can have.
o Identify the ways for such behaviors that can influence the cyber security, study vulnerabilities and security gaps that can be occurs due to such kind of behaviors
o Identifying the behavior of the Administrator and/or Operators to ensure SCADA operation are being completed properly
o If time and opportunity are available, research and test possible mitigation techniques as part of a mitigation strategy.
Research Questions
Criminals and hackers repeatedly deceive users to malwares exposure against their computers and connected networks.
Users and/or administrator have been expressed as the weakest link in security scheme [12] because of their behavior. For example countless studies have shown that users be likely to choose short and/or guessable passwords.
Possibly the most severe behavioral problem of system Administrators and Engineers is poor configuration of the system. This may be caused by failure to realize the security technology, or failure to follow the correct procedures [11]. Another problem seen is poor operating procedures e.g. not keeping the system up-to-date, not responding to security notices, poorly managing authentication and authorization schemes, and laziness.
Considering aforementioned facts in mind, following questions can be raised:
• What are the main mistakes for security being compromised in automation control systems?
• What are the main causes of these mistakes?
• What should be done to mitigate these causes?
METHODOLOGY
This chapter explains the general methodology adopted and research methods used in the project to gather the possible mistakes and the causes of such mistakes.
The project’s aim was to find out and mitigate mistakes along with their causes that influence installation, configuration and management of computer networks, operating system and SCADA1 applications. The first task was to identify the variables that are of importance, along with their possible values. These variables were essentially the mistakes committed by the administrators and engineers along with their causes. The important task here was to elicit the variables of importance as well as the relationships between these variables.
To achieve this task, the adopted methodology was divided into two main parts. The first part consisted of literature studies to identify mistakes. Appendix A (Section 10.1.1) provides list of these mistakes.
The second part was a set of interviews comprising of three phases which were based on the identified mistakes. These phases are shown in Figure 2. Interviews were used because these are the most common method of attaining probabilistic information. Although other sources are available which provide these information but they do not always have all the numbers required for the quantitative part of a probabilistic network [17]. The purpose of these interviews was to:
1. Phase I – List of possible causes for each of the mistakes identified earlier.
2. Phase II – The probability of the causes identified in Phase I.
3. Phase III – Conditional probabilities of mistakes based on the causes.
See Appendix A, Section 10.1.2 Questionnaire PHASE I, for list of causes. The data from th ese three phases were used to calculate the influence of each of the causes on the mistakes and the relationships between them.
The outcome of the literature studies and the three phase interviews were a set of data expressing mistakes, their causes and probabilistic values of the measure of their influence. This data were used to create a Bayesian Network for verification and analysis.
Bayesian Network is a graphical model to represent the relationships between variables. We used this gphical model for analysis as this method supports a complete and intuitive description of decision problems, stating both what is desired and what alternatives are available [15]. The data from the three phases were used in building a Bayesian Network. This was done to find the probabilities of each of the variables.
In the following sections we start with a subset of our problem, as an example, to introduce Bayesian Networks. And then the complete process is explained in detail.
Bayesian Networks
A Bayesian network is a graphical model that encodes probabilistic relationships among variables of interest [16]. For example, a Bayesian network could represent the probabilistic relationships between diseases and symptoms. Given symptoms, the network can be used to compute the probabilities of the presence of various diseases.
Bayesian Networks have been widely used in problem domains where the number of variables is indefinite and so are their values. Taking binary approach to figure out an outcome hasn’t always been applicable e.g. the possibility of firewall misconfigurations defined as 0, as in impossible or 1, as in possible.
For instance, in the outcomes for firewall misconfigurations, assume the amount of variables involved behind these outcomes such as how much resources organizations have, how well knowledge administrator have, how much complex configuration could be etc [15]. A Bayesian Network for this example is shown in Figure 4.
Figure 4 – Example Working of Bayesian Network
In the Figure 4 probability that a Firewall is misconfigured depend on the conditions (e.g. if the project is delivered under work stress). To define how these causes influence the probability one would have to set the attributes in the CPT3. In other words, for each combination of these causes a probability that a Firewall is misconfigured. i.e. P(Firewall misconfigured = True |Factor1,. ., FactorN). In given example, 8 (2N) probabilities need to be asked from the respondent (to get the 16 probabilities).
There can, however, be numerous factors that influence these mistakes. To gather and then to reduce these causes we iteratively interviewed, to come up with a compact and precise list of mistakes. First causes of misconfigured Firewall have been collected and obtain a long list of respondent opinions. Then the list was ordered and the main causes for each type of mistake identified. Finally most relevant causes were chosen to reduce the size of CPT. These dimensionality reduction were necessary, else there would be a numerous factors for a respondent to answer, as well to remove repetition.
Experts were asked to specify a numeric value for probability distribution over a variable’s (let’s call it V) states. So we can say, what is the probability of causes being “True” and “False” respectively. Probability distribution is influenced by given factors (say A1, A2 and A3). In given example, arrow has been drawn from the factors that influence the variable. Hence, from A1, A2 and A3 to V
The Table 1 was produced from GeNIe4. It shows the different states for each combination of different factors. Each variable can be in True of False state. So there will be 8 different combinations, as discussed above.
The questions asked to experts, in this case, were the probabilities P1 to P8. These represent a probability for V being “True” given A1, A2 and A3 are in a certain states. So for example, P2 should be the probability P(V=True | A1=True, A2=True and A3= False). In clear text: “How probable is it that V is True if A1 is True, A2 is True and A3 is False).
Hence we get, for all possible combinations of states for given factors that influence V, what is the probability that V is True. The probability for V is False can be calculated by taking difference of 1.
P1 should be the probability P(V=True | A1=True, A2=True and A3= True)
P2 should be the probability P(V=True | A1=True, A2=True and A3= False)
P3 should be the probability P(V=True | A1=True, A2=False and A3= True)
P4 should be the probability P(V=True | A1=True, A2=False and A3= False)
P5 should be the probability P(V=True | A1=False, A2=True and A3= True)
P6 should be the probability P(V=True | A1=False, A2=True and A3= False)
P7 should be the probability P(V=True | A1=False, A2=False and A3= True)
P8 should be the probability P(V=True | A1=False, A2=False and A3= False)
Mistakes Identified from Literature Studies
The cyber security aspect of SCADA systems has been widely discussed in books, publications, seminars and whitepapers. The same were used to collect probable mistakes to attain project’s objectives. These mistakes are discussed in detail in section 6 of this report. The source of this information was several institutions working on related issues. A list of these institutions is presented as Appendix B Section 11.1, to this report.
These institutions were chosen due to their work done in cyber security of control systems including SCADA. They continuously publish latest threats, probable mistakes leads to vulnerabilities, reports and articles on relevant scope. These publications include common vulnerabilities existing in SCADA systems, best practices to eliminate those vulnerabilities or at least make them hard for the attackers to exploit and so forth. This data significantly helped in identification of mistakes and preparing questionnaires. These also helped to get the knowledge from experts about human negligence of installation, configurations, operations and management of computer network and SCADA Applications. List of mistakes identified in this phase, and questionnaire based on them are listen in Appendix A, List of Mistakes. A series of interviews were conducted using this questionnaire.
Interviews and Data Analysis Phase
On the basis of mistakes, interviews with the experts were conducted to get the probable list of causes. This is primarily common method to get probabilistic information [17]. Hard copy of questionnaire was presented during a face-to-face interview.
The experts include, Managers (those are involved in all phases of project), Security Experts (responsible for cyber security in SCADA system) and System Engineers (responsible of installation, configuration and management of the SCADA system). It was important to reach all these personnel to find the causes of probable mistakes made at some point in the projects since Managers who are involved in different projects from start till shipment have their own expert opinion. Security experts on the other hand, design security policies. System Engineers are involved in operation and implementation of the designed policy on system. They have their own observations on system’s efficiency or deficiency in response to the new policy.
There were a total of eight experts within the same organization, who took part in the interview. Of all the participants there were seven male and one female. They were between 30 and 60 years old. All experts were from engineering background with extensive experience in SCADA system.
Table of contents :
1 INTRODUCTION
2 BACKGROUND
2.1 SCADA
3 RESEARCH PURPOSE, PROBLEMS AND GOALS
3.1 Project Purpose
3.2 Problem Domain
3.3 Goals
3.4 Research Questions
4 METHODOLOGY
4.1 Bayesian Networks
4.2 Mistakes Identified from Literature Studies
4.3 Interviews and Data Analysis Phase
4.3.1 Experts Profile
4.3.2 Phase I – Gathering Causes of Mistakes
4.3.2.1 Grouping of Similar Causes
4.3.3 Phase II – Probabilities of Causes
4.3.4 Phase III – Probability of Mistakes Using Conditional Probability Table
5 LITERATURE REVIEW – MISTAKES CAUSED BY HUMAN CARELESSNESS
5.1 List of Mistakes
5.1.1 Firewalls, IDS, Routers and Switches are Misconfigured
5.1.2 Issues regarding Network Design, Installation and configuration of operating system and software used in SCADA and/or corporate network
5.1.3 Ports and Services Remains Open after Installation of Operating System or Application
5.1.4 Wireless Link in Computer Network are Misconfigured
5.1.5 Default Setting of Devices are not Changed when Configuring
5.1.6 System Maintenance, Modification and Testing are not Completed Correctly
5.1.7 Access Control Policies in Computer Networks are not Implemented Correctly
5.1.8 Taking and restoration of backups are completed incorrectly
5.1.9 Updates and Patches of Operating System and Antivirus are not Manage Properly
5.1.10 Supporting Services or Facilities not Managed Properly
5.1.11 Improper Management of Peripheral Devices
5.1.12 Strong Password Policy is not Implemented Correctly and/or Password is Written down on Papers
5.1.13 Log Management not Completed Properly
5.1.14 Sensitive Information is Disclosed from Technical Staff by Means of Social Engineering
6 SURVEY RESULT AND ANALYSIS
6.1 Bayesian Model of Identified Causes and Mistakes
6.1.1 Identified Causes
6.1.2 Identified Mistakes
6.1.3 Influence of Causes on Mistakes
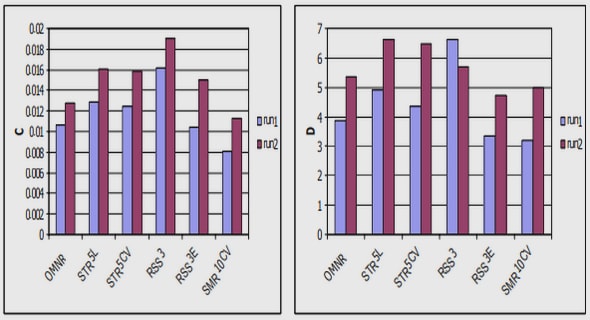
6.1.4 Validation of Results
6.1.5 Validate Effect of Presence of Causes
6.1.6 Validate Effect of Absesnce of Causes
6.1.7 Strength of Influence
7 MITIGATIONS
8 CONCLUSION
9 REFERENCE
10 APPENDIX A: SURVEY
10.1.1 List of Mistakes
10.1.2 Questionnaire Phase I, List of Causes
10.1.3 Questionnaire Phase I, Grouping of Similar Causes
10.1.4 Compilation of Questionnaire Phase I
10.2 Questionnaire Phase II, Priority/Ranking of Causes
10.3 Questionnaire Phase III, Conditional Probability Table
11 APPENDIX B:
11.1 Supporting Literature
12 APPENDIX C: BASIC DEFINITIONS