Get Complete Project Material File(s) Now! »
Theoretical Framework
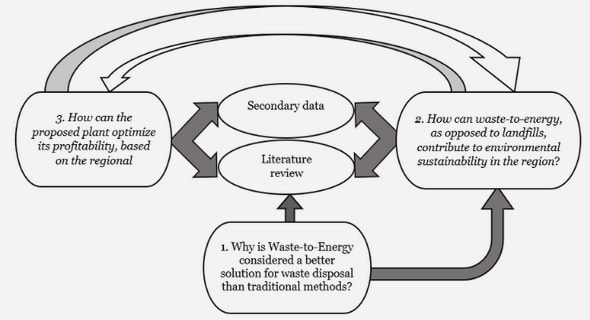
This section will cover important literature and theories already written. Through our research techniques we choose the following concepts to present: Steps in creating a successful Business Continuity Process, Training, Risk Management and Soft Systems Methodology. The displayed concepts will help to analyze our empirical data and draw the conclusions.
Steps in creating a successful Business Continuity Process
To establish a Business Continuity Plan there is a guideline to follow developed by Ka-rakasidis (1997) which consists of eleven components. These components are supposed to be used in conjunction with a risk management process. Hereby a brief explanation of the components will be presented:
- Obtain top management approval and support.
The managers need to support the BCP with the required resources and funds. They also need to fully understand and approve the plan in order to carry it out.
- Establish a business continuity planning (BCP) committee.
The committee is supposed to deal with the objectives and scope together with the de-velopment of the plan, but also to report, test, and maintain the business recovery processes.
- Perform business impact analyses.
The business impact analysis (BIA) is about the identification of the potential risks and how to carry out a preventive plan, together with the most reasonable resources. In order to perform an efficient impact analyses Wan (2009) suggests the following steps:
- Define assumptions and scope of project for which BIA is being conducted. Develop a survey or questionnaire to gather necessary information.
- Identify and notify the appropriate survey recipients. Distribute the survey and collect responses.
- Review completed surveys and conduct follow-up interviews with respondents as needed.
- Modify survey responses based on follow-up interviews. Analyze survey data.
- Verify results with respondents.
- Prepare report and findings to senior management.
- Evaluate critical needs and prioritize business requirements.
This stage is about the evaluation of processes and resources that are of need, in order to continue the business operations.
- Determine the business continuity strategy and associated recovery process.
This step is about reviewing the components and defining the recover strategy which can help the organization to restore from a failure.
- Prepare business continuity strategy and its implementation plan for executive man-agement approval.
Creating a manual with the necessary information about the strategies which can be rolled out for any department is of great importance. This will include the tasks, stan-dards, and responsibilities together with other details in order to recover from a failure.
- Prepare business recovery plan
With the help from a template all information and data concerning the recovery will be put into a larger plan.
- Develop the testing criteria and procedures.
This step can be seen as a plan for a training mechanism and is created to test and un-derstand how well the recovery plan works.
- Test the business recovery process and evaluate test results.
A key component is to have meetings regularly before, during, and after the implemen-tation of the plan in order to evaluate the business continuity plan. In this step the test-ing of the recovery procedures takes part.
- Develop/review service level agreement(s) (SLAs).
To reach a balanced service level agreement between two parties, in order to function synchronously.
- Update/revise the business recovery procedures and templates.
The continuous maintenance is done in order to prevent that all the procedures have to become redeveloped. Instead it is more efficient to continuously update the procedures by responding to changes, keeping the staff updated, and having an ongoing testing of the plan.
Training
Morwood (1998) distinguish between two different types of training best suited to busi-ness continuity training. These types are awareness training and scenario training.
Awareness training intends to give all members of the organization an appropriate level of understanding of the Business Continuity Plan. This type of training consists of two sub-division, introductory awareness training and detailed awareness training.
Introductory awareness training briefs all members of the organization who will have an indirect role in the execution of the Business Continuity Plan. In general, a 60 minutes session about the framework, strategies, and important procedures under the plan should be enough to inform the staff.
Detailed awareness training, in contrast, is aiming to educate the members of the organ-ization who will have a direct role in the execution of the business continuity plan. Morwood (1998) suggests that a half-day session should be sufficient to educate the staff about all aspects of the Business Continuity Plan. The information covered in this session is almost the same as in the introductory session, only more detailed. Another important part of the detailed awareness training is to focus on the precise roles and re-sponsibilities each staff member will have under the Business Continuity Plan.
In general, awareness training should be conducted for all members of the organization upon the establishment of the Business Continuity Plan or following significant changes to it. Moreover, it should be conducted for all newly hired employees and for those people who have moved into new positions or responsibility areas.
The second type of training is scenario training. Morwood (1998) suggests that this type of training should be conducted as a follow up of the awareness training. Scenario train-ing should be conducted at a level as appropriate as possible compared to the crisis or disaster situation. In Morwood’s approach scenario training includes practical exercises designed to confirm employees’ understanding of the Business Continuity Plan. Moreo-ver, it is aimed to raise their skill levels in the execution of the tasks and to identify po-tential weaknesses and issues relating to further development of the Business Continuity Plan.
Morwood (1998) divides scenario training into three distinct variants of training – desk-top exercises, call-out exercises, and operational exercises. Desk-top exercises are taken place within the office environment and participants are just required to assess and comment on how they would react to various scenarios. During call-out exercises par-ticipants are required to contact key staff members with responsibilities under the Busi-ness Continuity Plan and confirm their availability and recall time. Operational exercis-es will be practiced with full operational response to the exercise scenario. The Business Continuity Plan will be physically implemented by the exercise participants. Due to cost issues, normally, the activation of outside resources is not involved in the training ses-sions.
Risk Management
“A risk is a potential problem, a situation that, if it materializes, will adversely affect the project. Risks that materialize are no longer risks, they are problems”. “All projects have risks, and all risks are ultimately handled. Some disappear, some develop into problems that demand attention, and a few escalate into crises that destroy projects and careers. The goal of risk management is to ensure that risks never fall into the third cat-egory”. (Hallows, 2005 p.96)
“A risk is a possible unplanned event. It can be positive or negative. In project man-agement the success of our projects depends on our ability to predict a particular out-come. Since risks are the unpredictable part of the project, it is important for us to be able to control them as much as possible and make them as predictable as possible.” (Newell & Marina, 2004 p.174)
Risks can be divided into two categories – known risks and unknown risks. Known risks are risks that can be identified and unknown risks are those risks that cannot be pre-dicted at all. A threat or a pure risk can only have a negative possibility as a result. In contrast an opportunity is a risk that can only have positive outcomes. Business risks are considered as normal risks of doing business and can both have good and bad outcomes.
Risks occur in all companies, therefore an important aspect of managing and minimiz-ing risks is known as “Risk Management”. The International Federation of Risk and In-surance Management Associations (IFRIMA), the international umbrella organization for risk management associations throughout the world, says that risk management is a central part of any organization’s strategic management (Reuvid, 2007). Risk manage-ment is the process of identifying, categorizing, responding to risks strategically, and managing the risks. This process is also known as enterprise risk management (ERM). The initial focus in risk management should be on identifying the risks. These risks can be factors that cause time delays or impede the usual way of working in an organization. According to Hallows (2005), the most common risks that an organization can encoun-ter are:
Staff Risks
- Key staff will not be available when needed
- Key skill sets will not be available when needed Staff will be lost during the project
Equipment Risks
- Required equipment will not be delivered on time Access to hardware will be restricted
- Equipment will fail
Client Risks
- Client resources will not be made available as required Client staff will not reach decisions in a timely manner
- Deliverables will not be reviewed according to the schedule
- Knowledgeable client staff will be replaced by those less qualified
Scope Risks
- Requirements for additional effort will surface
- Changes of scope will be deemed to be included in the project
- Scope changes will be introduced without the knowledge of project management
Technology Risks
- The technology will have technical or performance limitations that endanger the project
- Technology components will not be easily integrated
- The technology is new and poorly understood
Delivery Risks
- System response time will not be adequate
- System capacity requirements will exceed available capacity The system will fail to meet functional requirements
Physical Risks
- The office will be damaged by fire, flood, or other catastrophe A computer virus will infect the development system
- A team member will steal confidential material and make it available to com-petitors of the client (Hallows, 2005 p.97
Analyzing information available from previous cases will be valuable and helpful in identifying risks in the current organization. A structured review of previous cases should be done as a part of the identification process. Individuals both inside and out-side the organization will also be useful for the risk identification process. Risk identifi-cation process often involves large numbers of individuals, it is therefore recommended to use different group techniques such as:
Delphi Technique: In the Delphi technique the participants are usually anonymous. By having anonymous participants, problems such as negative effects of face-to-face dis-cussions or individuals that dominate the process by using their authority or position are avoided. In this technique the facilitator asks for input from the participants, in the form of answers to questionnaires and their comments to these answers. The contributions are then summarized by the facilitator into a list that is send to each participant. The partici-pants then add additional thoughts to the summarized list. This process continues until there are no more thoughts generated. This technique can be conducted using any form of communication technology such as e-mail or telephone. One of the advantages of the Delphi technique is that the individuals can participate from many different locations.
Brainstorming Technique: The Brainstorming technique is one of the most common group dynamics techniques. In the brainstorming technique a group of participants are summoned to a meeting. The participants are then asked by the facilitator to name any risk that they can think of, no matter their significance. The risks are then listed by the facilitator on a board. The main purpose of the brainstorming technique is to create a kind of chain reaction of identification of risks. For example the ideas generated by one participant will generate new ideas from another participant. The downside of brains-torming technique is that the whole process is dependent on an excellent facilitator. If the process lacks a good facilitator there will be minimum involvement from the partic-ipants. This downside will even get bigger if there is a big difference in the status of the participating individuals. An individual who has more authority may dominate the meeting with his thoughts and ideas.
The second part of the risk management process is dealing with categorizing the risks. Risk categorization is the process of evaluating the risks that have been identified. The purpose of categorizing the risks is to set up a way of classifying the risks in the order of their importance. Several statistical methods of defining the degree of risk exists, but the simplest and most effective method is to depict risks as high, medium or low. The level of the risk depends on two characteristics; the probability and the impact of the risk. The probability and the impact of the risk can be evaluated on a scale of one to ten. When the impact and the probability value are multiplied together the result will represent the expected severity value of the risk. Figure 3.1 and 3.2 illustrates a method of determining the degree of a risk.
1 Introduction
1.1 Background.
1.2 Problem Discussion
1.3 Research Questions
1.4 Purpose
1.5 Perspective
1.6 Delimitations
1.7 Definitions
1.8 Interested parties
2 Methodology .
2.1 Scientific approach
2.2 Research philosophy
2.3 Research approach
2.4 Research strategies
2.5 Time horizon
2.6 Literature search strategy
2.7 Literature review
2.8 Reliability and validity
2.9 Generalizability
2.10 Objectivity
2.11 Data collection techniques
3 Theoretical Framework
3.1 Steps in creating a successful Business Continuity Process
3.2 Training
3.3 Risk Management
3.4 Soft systems methodology
3.5 Reflections from the theoretical framework
4 Empirical findings
4.1 Case observation
4.2 Interviews
5 Analysis
5.1 Categorization of problems
5.2 Risk Evaluation
5.3 Problem relation analysis
5.4 Suggested components to become resilient
6 Conclusion
6.1 Fulfilling the purpose
6.2 Future research
References
Appendix
GET THE COMPLETE PROJECT
The need for a developed Business Continuity Plan