Get Complete Project Material File(s) Now! »
Information Security Awareness and Training (ISAT)
The context and the importance of ISAT is described in a series of standards that are widely implemented by enterprises and organizations globally, as in ISO 27000 series and NIST SP-800 publications. Nieles et al. (2017) mention that the human factor can be the weakest link in information security systems, where utilizing ISAT can aid users to perform their tasks in a more secure way. In addition, the ISO/IEC 27002 highlights the importance of ISAT and how imperative is to be implemented iteratively (ISO/IEC 27002, 2013). ISAT is a prerequisite for a series of a certificates in standards as ISO/IEC 27001, COBIT, Payment Card Industries – Data security and ISO 9001: 2000 (Stefaniuk, 2020).
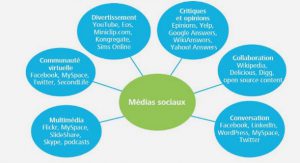
According to some researchers there are three main categories that ISAT can be categorized, conventional, instructor led and online (Alotaibi & Alfehaid, 2018). The first category includes methods as posters, stickers, leaflets and employee newsletters (Alotaibi & Alfehaid, 2018; Stefaniuk, 2020). Instructor led is based on formal presentations or training sessions in classrooms regarding information security policy and procedures (Alotaibi & Alfehaid, 2018; Stefaniuk, 2020). Online ISAT can be implemented utilizing electronic articles or emails, web based security awareness triaging, security alert messages, video clips, social media, online discussion groups (forums) and serious games (Alotaibi & Alfehaid, 2018; Stefaniuk, 2020).
Lockheed Martin Cyber Kill Chain
Lockheed Martin Corporation, a well known aerospace, arms and defense, security and advanced technologies company, motivated by the emergence of the Advanced Persistent Threats (APTs), developed the “Intelligence-driven Computer Network Defense” model (Hutchins et al., 2011). Since APTs are launched by adversaries using advanced tools and techniques and devoting a lot of time for their preparation and their attacks, conventional countermeasures are insufficient (Hutchins et al., 2011). This model incorporates a risk management strategy with emphasis on the skills and the purposes of the attackers (Hutchins et al., 2011). The Lockheed Martin Cyber Kill Chain (LM CKC) framework is an essential element of the model, analyzing the intrusions and affecting the counteractions of the defense IT team and is comprised of several phases (Hutchins et al., 2011). Methodologies based on a series of steps have previously been applied for military purposes and in IS, that are more concentrated on actions launched after the intrusion, while the LM CKC is based on early detection and mitigation of the cyber response personnel (Hutchins et al., 2011).
The CKC is divided in seven steps, where the attacker in order to succeed must overcome all, whereas the defender’s countermeasures can be launched and block the attack even in one of them (Lockheed Martin, 2015). These steps are summarized in Figure 1 and are analyzed as follows:
1. Reconnaissance: At this stage the adversaries before launching their attack, they execute research and try to identify and select the targets, planning their operation (Hutchins et al., 2011; Lockheed Martin, 2015). Therefore, they use primarily social media to identify employees, harvest any available corporate email accounts and focus on detecting any servers directly connected to the internet (Lockheed Martin, 2015). This phase can be divided to passive Reconnaissance, where the adversaries act without compromising their detection, and active Reconnaissance, where their methodology endangers their operation, by notifying the defender’s IS team with their activity (Yadav & Rao, 2015). Passive Reconnaissance can be facilitated by searching domain names or retrieving information via social media or public records, while active Reconnaissance requires techniques as port scanning (Yadav & Rao, 2015). Since detecting this phase is extremely difficult, the defender’s IS team can rely on website corporate logs and enhancing alerting on users that might be prone on attacks (Lockheed Martin, 2015).
2. Weaponize: This phase acts as the preparation phase, where the adversaries develop the malware, using automated tools, and form their penetration plan, based on the data gathered during the Reconnaissance phase (Hutchins et al., 2011; Yadav & Rao, 2015). The functionality of the malware relies on a remote access tool (RAT), which provides remote access to the attacker, and an exploit, which exploits the vulnerabilities of the target’s system, in order for the RAT to be executed without being detected (Yadav & Rao, 2015). While the defender cannot prevent this phase from occurring, a full malware analysis accompanied by the timeline and a metadata analysis can provide with useful information on how to address such incidents (Lockheed Martin, 2015).
3. Delivery: The adversaries launch their attack at this phase, delivering the malware to the target, which in most cases is applied through malicious email attachments, phishing attacks, websites and web servers, USB removable media or social media (Hutchins et al., 2011; Lockheed Martin, 2015; Yadav & Rao, 2015). Crucial part in a successful mitigation effort is to analyze the delivery phase, investigating the systems and people used as a means for initiating the attack (Lockheed Martin, 2015).
4. Exploitation: At this phase the adversaries gain access to the targeted system, after having successfully delivered their cyber weapon (Hutchins et al., 2011; Lockheed Martin, 2015). In order for the payload of the weapon to be executed, it must be used on the specific outdated Operating System, for which it was created and remain undetected by any anti-malware software safeguarding the defender’s system (Yadav & Rao, 2015). Exploit is a crucial phase, from a technical point of view, because the cyber weapon must be customized to the defender’s system vulnerabilities (Yadav & Rao, 2015). This phase can be triggered by the attacker exploiting the weaknesses of a server or by a victim who is deceived and carried away into actions described in the Delivery phase, as clicking on email attachments (Lockheed Martin, 2015). Penetration testing and hardening measures can facilitate the IT defense team to block the attack (Lockheed Martin, 2015). Moreover, a sophisticated anti-malware software can detect the exploit or payload statically or dynamically scan, during run time and prevent the ongoing attack (Yadav & Rao, 2015).
5. Installation: During this phase the malicious users install a remote access trojan or backdoor on the compromised system to maintain their unauthorized access to the system (Hutchins et al., 2011). The adversaries have developed several techniques to avoid detection by antivirus or Intrusion Detection Systems (IDSs) utilizing specific tools that disable them (Hutchins et al., 2011). 6. Command and Control (C2): The adversaries are establishing a C2 channel gaining remote access inside the victim’s IT infrastructure, via web, DNS or email protocols (Hutchins et al., 2011; Lockheed Martin, 2015). Such communication can be achieved through a centralized structure, where the traditional client-server model applies, a decentralized structure, where large botnets can be manipulated using peer-to-peer P2P architecture and a social network based structure, where the possibilities of social media are employed (Yadav & Rao, 2015). In order to remain undetected for as long as possible, the attackers try to masquerade the communication between the victim’s system and their own using TOR services and protect their server from being discovered from any IS response team (Yadav & Rao, 2015). On the other hand, the defender can focus on blocking a C2 channel by network hardening and perform malware analysis in order to trace the attack to the point of origin (Lockheed Martin, 2015).
7. Actions on Objectives: This is the final phase of the CKC, where adversaries can afterwards execute their malicious activity and defenders have a last opportunity to block the attack and protect their systems (Hutchins et al., 2011). At this point the intruders can accomplish the purpose of their attack and control all the crucial victim’s systems, collecting and exfiltrating data, tampering with data or resources or even use them for another cyber incident as a part of their botnet (Hutchins et al., 2011; Lockheed Martin, 2015). Upon discovery, the incident response team must act immediately to block the attack and analyze the inflicted damage, by trying to detect the unauthorized network activity and communication (Lockheed Martin, 2015).
As previously analyzed there is a series of tools and methodologies for the defenders during the CKC that can be implemented at each phase and response accordingly to the adversaries. However, in order to be able to defend more adequately from similar future attacks, the IS response team must execute an intrusion reconstruction (Hutchins et al., 2011). This technique includes the reverse analysis of the phases of the CKC that preceded the detection of the attack to investigate the actions of the attackers that bypassed the enforced security mechanisms (Hutchins et al., 2011). Thus, the CKC is a model which can offer high standards of protection, can be utilized from the IS teams to constantly decrease the risk of an intrusion and offer a guidance on learning and adapting to the emerging threats.
Searching for the literature
Since the goal of this thesis is to extract information of articles that analyze ISAT serious games, there was a preliminary search to detect which common keywords could lead to this result. Thus, based on the findings of the title of the articles, keywords as game(s), information, cyber, security, awareness, training should be absolutely be a part of the search process. However, all of the above words have a very wide definition and if used sparsely the outcome can be extremely broad, compromising the search and subsequently the screening process, by returning a huge amount of unrelated to the research question articles and wasting time by excluding them. Therefore, a selected combination of the previous keywords was appropriate to focus on serious games cyber-related and ignore all types of other games. Because of the preliminary search, a number of other keywords were identified as un-related to the purpose of this study and they were explicitly excluded to further limit the searching process. This judgment was carefully decided in order to facilitate the searching and screening process, without undermining the quality of the research. After the initial research and without using the selection criteria the search in Google Scholar came up with with following results, according to each Boolean keyword combination, as previously analyzed:
1. Combination 1: game and (threat or attack or attacks or “information security” or cyber or cybersecurity or awareness) not (« game theory » or Stackelberg or « game theoretic » or « game theoretical » or stochastic or « attack-defense »): about 61,900 articles (20/02/2021).
2. Combination 2: games and (threat or attack or attacks or “information security” or cyber or cybersecurity or awareness)) not (“game theory » or Stackelberg or « game theoretic » or « game theoretical » or stochastic or « attack-defense » or game): about 25,300 articles (20/02/2021).
3. Combination 3: gamification and (threat or attack or attacks or “information security” or cyber or cybersecurity or awareness)) not (“game theory » or Stackelberg or « game theoretic » or « game theoretical » or stochastic or « attack-defense » or game or games): about 966 articles (20/02/2021).
4. Combination 4: gamified and (threat or attack or attacks or “information security” or cyber or cybersecurity or awareness)) not (“game theory » or Stackelberg or « game theoretic » or « game theoretical » or stochastic or « attack-defense » or game or games or gamification): about 70 articles (20/02/2021).
5. Combination 5: training and (threat or attack or attacks or “information security” or cyber or cybersecurity or awareness)) not (“game theory » or Stackelberg or « game theoretic » or « game theoretical » or stochastic or « attack-defense » or game or games or gamification or gamified): about 113,000 articles (22/02/2021).
6. Combination 6: cyber and range not (training or game or games or gamification or gamified): about 385,000 articles (23/02/2021).
Practical screen
The practical screening of the literature study was completed in three phases as follows:
Phase 1: The search is conducted by limiting the use of keywords in the title of articles, excluding citations and patents. Moreover, the timeframe was selected according to the protocol, for articles published within the last 5 years of this study (since 2016).
Phase 2: The output of the search was further restricted to articles from journals and conferences, written in English language and screened based on the content of the title, to usable, in accordance with the research question. Articles that were selected in Phase 2 were stored in 6 separate folders in Zotero, according to the keyword search, that is analyzed in Section 3.2.1 respectively.
Phase 3: All articles from Phase 2 were screened further by reviewing their abstract, to limit articles that can answer to the research question more efficiently, excluding articles referring entirely to education (primary schools, high schools, university courses), literature reviews, physical serious games, game theory or other articles that were irrelevant. Every article of Phase 2 was stored in the appropriate subfolder in Zotero, in accordance with its relevance to the study.
Synthesis of studies and Writing the review
As previously mentioned in the protocol in section 3.1.1, this literature study follows a thematic synthesis based on codes of the qualitative data, which will result in generating themes. The codes are based on the filled forms of each article, where every entry on the field of Type of Defense, that was implemented during Data Extraction, is a code. Some codes are unique, whereas others are common in different articles. The identified codes (Type of Defense) can generate the themes of the study by mapping them out against the appropriate step of the CKC which are stored in the field LM CKC, as described in section 3.3.2 (Data Extraction). Thus, each code can be attributed to one of the seven steps of the CKC and each theme contains one or more codes of the same or different studies that are analyzed in the articles and are presented in a narrative way. Each step of the CKC is a main theme and synthesized into a subsection in the results section, while some of the steps can be comprised of sub-themes that follow the same pattern and are presented in every applicable section.
Table of contents :
1. Introduction
1.1. Problem Statement & Research Question
1.2. Purpose and Significance of the Thesis
1.3. Research Field / Theme / Scope
1.4. Structure of the Thesis
2. Theory
2.1. Information Security
2.1.1. Information Security Awareness and Training (ISAT)
2.2. Lockheed Martin Cyber Kill Chain
2.3. Related Work
3. Research Method
3.1. Planning
3.1.1. Protocol:
3.2. Selection
3.2.1. Searching for the literature
3.2.2. Practical screen
3.3. Extraction
3.3.1. Quality appraisal
3.3.2. Data extraction:
3.4. Execution
3.4.1. Synthesis of studies and Writing the review
3.5. Research Tools
4. Article Overview
5. Results
5.1. Reconnaissance
5.2. Weaponization
5.3. Delivery
5.4. Exploitation
5.5. Installation
5.6. Command and Control (C2)
5.7. Actions on Objectives
6. Discussion
6.1. Limitations of the research
6.2. Future Research Reccomendations
7. Conclusion
References