Get Complete Project Material File(s) Now! »
Chapter 3 Security Challenges During OSS Migrations
Introduction
The rudimentary management framework is proposed in the previous chapter as a result of reviewing the literature and conceptualising the categories obtained from the literature in order to develop such framework. In this chapter, the main focus is on establishing a need for developing a model that can be used to address the security challenges during closed source software to OSS migrations. The rudimentary framework will be augumented with the security aspects in this chapter.
The layout of the chapter is as follows: section 3.2 compares OSS and CSS security. The security challenges in OSS are explored in section 3.3 while section 3.4 explains the challenges during migrating from closed source to open source. A model is proposed to address a number of security challenges during the migration from CSS to OSS (see section 3.5). The model is synthesised from the framework proposed by Aner & Cid (2010) and will augument the rudimentary framework to protect sensitive information during system migrations, suggested in Chapter 2. How the model can be implemented is explored in section 3.6 while section 3.7 concludes the chapter. The content of this chapter was synthesised into a research publication (Ajigini et al. 2014).
Comparing OSS and CSS Security
Hansen et al. (2002) emphasise the importance of analysing a whole OSS system when performing an extensive security investigation. Such analyses include the application software, its source code, and the tools used for developing the object code. Examples are compilers, operating systems, hardware and the whole development environment.
Different authors have different perceptions when they compare OSS security with that of CSS as shown in Table 3-1. The table reveals that the security of OSS is far beter than that of a CSS system.
Discussion of Table 3-1
Closed source designs and protocols are not published, whereas the OSS designs and protocols are published enhancing the security of OSS programs since logical errors may be revealed (Hoepman and Jacobs 2007). This is also the view of some authors (Dwan 2004; Manthena 2011; Schryen 2011) that it is easier to find and correct errors in OSS than in CSS because of the openness of OSS code. OSS users have the freedom to validate and test the code in order to ascertain its quality and security, therefore OSS initial coding tends to have higher quality and security than CSS (Manfield-Devine 2008).
CSS is perceived to be more secure than OSS because it is developed in a controlled environment by a dedicated team of developers with a common direction (Walia et al. 2006 ; Daniel 2009; Pokarna et al. 2015). Moreover OSS is considered to be reliable equally as CSS and the time to fix security vulnerabilities is twice as quickly than CSS (Singh et al. 2015), although Hansen et al. (2002) contend that CSS can be as secure as OSS because the security of software is dependent on the user and not on its openness or closedness.
The severity of vulnerabilities found between OSS and CSS is similar (Schryen 2009). Furthermore, more and faster patches are found in OSS whereas patches are not released as fast in CSS, thereby increasing the risk of using the system securely (Hoepman and Jacobs 2007). OSS improves the software transparency, security and trustworthiness howevver the security of CSS is dependent on the user and not necessarily its closedness or openness (Hansen et al. 2002; Circoria et al. 2012).
OSS is more secure than CSS as illustrated in this section. However, organisations have to consider security challenges when migrating from CSS to OSS because there are security challenges that have to be overcome when migrating from a closed system to an open system (Geetha 2012). Risk management systems and other security monitoring tools are part of the management framework developed in this thesis. Thus, the management framework developed in this thesis may assist in managing the security challenges during software migrations.
Security Challenges in OSS
While OSS offers a number of advantages, notably cost efficiency and reduced vendor lock-in, it does, however, raise a number of security concerns. Some security concerns regarding the migration from proprietary platforms to OSS platforms are phishing, stealing sensitive information, e.g. account details and cookies and getting hacked during the process (Mtsweni & Bierman 2008).
The problem of the security of OSS was highlighted by two events, namely, a report released by Fortify Software in July 2008 (Open Source Security Study Fortify Report 2008), claiming that necessary standards were not achieved by OSS developers, and that Linux kernel developers had covered up security vulnerabilities (Manfield-Devine 2008). It was recommended in Fortify’s report that OSS should be viewed warily due to alleged high risks involved by government and commercial organizations. The report further recommended the conducting of risk analyses and code reviews on any OSS code that runs in business-critical applications.
According to Manfield-Devine (2008), the US Department of Homeland Security, which is part of the US government’s Open Source Hardening Project, backed Coverity Software (Open Source Coverity Report 2008) to investigate security issues affecting OSS products, and they produced a report that disagreed with the Fortify findings. Coverity Software analyzed 55 million lines of code across 250 projects (amongst others Linux and Apache) and concluded that OSS quality and security are improving.
Some of the Security Challenges in OSS include:
style= »list-style-type: none; »
Linux Security Concerns: According to the US National Security Agency (NSA), Linux security has been enhanced to cater for access controls, but they acknowledge that more work is still required to make SE Linux a trusted operating system that meets requirements of governments or corporate users (NSA 2001). To enhance the security of Linux, the NSA informed Linus Torvalds to add backdoors into Linux (Engstrom 2013).
Breaches of secrecy/unauthorised access: According to the Danish Board of Technology Working Group (Danish Board of Technology Working Group 2002), security in OSS for e-government includes protection against breaches of secrecy in the content of data communication (e.g. sensitive personal data, members of the public and companies’ economic circumstances) and protection against unauthorised access to computers (e.g. destruction of data or hacking of websites).
Lack of Linux security: From an analysis performed by Mi2g, it was found that Linux-based web server systems were increasingly attacked by system hackers and it was found that in the first six months of 2002, there was a 27% increase in successful system attacks (Mi2g Report 2002). Subsequently, Fitzgerald and Bassett (2003) have suggested that Open Source Software should not be used by highly security sensitive users and also not for critical systems. However, this view no longer holds since OSS quality has improved significantly since then (Silic & Back 2015; Pokarna et al. 2015).
Chapter 1 Introduction
1.1 Purpose of the Research
1.2 Research Questions
1.3 Delineations of the Research
1.4 Value of the Research (Rationale)
1.5 Research Design and Methodology
1.6 Contributions of this research
1.7 From Rudimentary Management Framework to Final Management Framework
1.8 Chapter Layout of the Thesis
1.9 Conclusion
Chapter 2 The Rudimentary Management Framework
2.1 Introduction
2.2 What is Sensitive Information?
2.3 Management of Sensitive Information
2.4 Protection of Sensitive Information
2.5 Information Sensitivity and Information Classification
2.6 What is Open Source Software (OSS)?
2.7 What is Closed Source Software (CSS)?
2.8 Overview of Platform Migrations
2.9 Most Popular OSS Projects
2.10 Benefits of OSS vs. CSS – a comparison
2.11 OSS Initiatives
2.12 Addressing OSS Security
2.13 Properties of a Management Framework
2.14 Towards a Rudimentary Management Framework
2.15 Conclusion
Chapter 3 Security Challenges During OSS Migrations
3.1 Introduction
3.2 Comparing OSS and CSS Security
3.3 Security Challenges in OSS
3.4 Challenges during the Migration from Proprietary to OSS Platform
3.5 A Model for Addressing the Security Challenges during Migration to OSS
3.6 Implementing the Proposed Model
3.7 Conclusion
Chapter 4 Research Design and Methodology
4.1 Introduction
4.2 Philosophical Perspectives
4.3 Research Methods
4.4 Research Methodology
4.5 Data Collection
4.6 Data Analysis
4.7 Conclusion
Chapter 5 Preliminary Management Framework: Quantitative Data Analysis
5.1 Introduction
5.2 Biographical Data Distributions
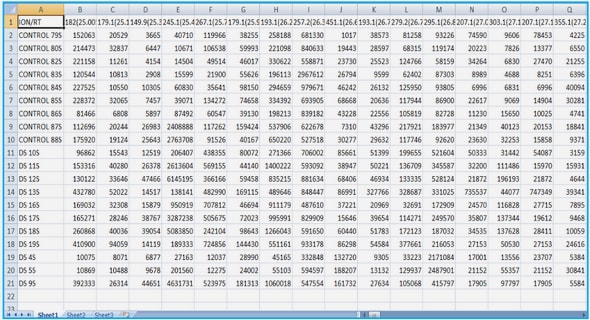
5.3 Identifying Constructs using Factor Analysis
5.4 Reliability Analysis of the Ten Sub-Constructs
5.5 Description of the Sub-Constructs
5.6 Calculation and Comparison of the Sub-Construct Scores
5.7 Exploratory Factor Analysis of the Ten Sub-Constructs
5.8 Reliability of the Four Main Constructs
5.9 The Distributions of the Four Main Constructs
5.10 Multivariate Correlations of the Four Main Constructs
5.11 Resulting Framework from the Quantitative Analysis
5.12 Validity and Reliability in Quantitative Research
5.13 Conclusion
Chapter 6 Final Management Framework: Qualitative Data Analysis
6.1 Introduction
6.2 Validity and Reliability in Qualitative Research
6.3 Qualitative Data Analysis Steps
6.4 Interview Narratives
6.5 Categorisation of Information (Nodes Identification)
6.6 Management Framework on Information Sensitivity during Software Migrations
6.7 Ethical Considerations
6.8 Conclusion
Chapter 7 Conclusion and Recommendations for Future Work
7.1 Introduction
7.2 Limitations of the Research
7.3 Synopsis of the Research Questions
7.4 Synopsis of the Thesis Chapters
Recommendations for Future Work
References
GET THE COMPLETE PROJECT
A FRAMEWORK TO MANAGE SENSITIVE INFORMATION DURING ITS MIGRATION BETWEEN SOFTWARE PLATFORMS