Get Complete Project Material File(s) Now! »
Rationale and Resilience
mtd rationale MTD acknowledges the fact that vulnerabilities are present in any system and that cyber attackers with enough time will, eventually, find and exploit them. MTD’s goal is to make the task of finding and exploiting a vulnerability more resource-consuming for the attackers, as compared to a non-MTD version of the system. MTD proposes to achieve this by constantly changing some of the system’s components that, in turn, will also imply changing the system’s attack surface.
“A system’s attack surface is the subset of the system’s resources that an attacker can use to attack the system.” [75] The attack surface ’movement’ makes that the information an at-tacker gathered about the system is now limited in time. Thus, a discovered and then crafted attack at a given time t0, might not work when the attacker launches it later at t0 + Dt; because the target system is no longer the same: the attack surface changed, and the vector of attack may no longer be valid. MTD contrasts with systems’ security measures that try to keep the attack surface small (i.e., attack surface reduction). MTD acknowledges that defenders do not entirely know the attack surface. Thus, those unknown vectors of attack can not be reduced in number (nor quality), but they can be ’moved’. resilience MTD’s founding document [34] states that the exploit of a vulnerability shall not prevent the MTD system to provide its service, and, even if exploited once, it will not be able to be exploited again. This is a desirable characteristic for cyber resilient systems.
A Brief History of MTD
pre-history The concept of changing system components to pre-vent unintended parties to disrupt its purpose is not new. Applications of this concept can be tracked in modern science at least to more than one hundred years ago in a patent of N. Tesla [174]1. Particularly, the World War II (WWII) produced several advances in these kind of applications for communication systems (e.g., the Enigma machine, SIGSALY). This WWII setting also layed the foundations of modern cryptography-cryptology enabled by the Colossus computers [148]. Applications of the concept of defense through constant change in the Internet era can also be found at least since 2001 [84]. However, is not until the last decade that the term « Moving Target Defense » was coined and emerged as a cyberdefense paradigm.
milestones and publications trend The MTD paradigm was proposed in 2009 in the context of a U.S. National Cyber-Defense Summit [34] with support of the Federal Networking and Information Technology Research and Development (NITRD) Program. Since then, MTD has been an important topic in cyberdefense with more than 500 scientific publications as of September 2020. Fig. 2.1 illustrates the number of scientific publications about MTD per year2. We can observe an upper-trend in the number of publications per year. We present a non-exhaustive chronology of MTD milestones in Table 2.1.
Fundamentals, Techniques, and Taxonomies
The MTD literature can be divided into three fields [28]: Theory [67, 204–206], Evaluation [68, 132, 173, 198], and Strategy [28, 33, 100, 128, 160, 190, 203]. The Strategy field covers concrete MTD techniques that can be implemented in real systems. This thesis will largely focus on this field, which we review after the two others. theory and evaluation MTD Theory deals with mathematical-analytical theory, systems and attacker models, and theoretical tools to formally discuss about MTD. R. Zuang et al. defined three components that constitute the foundations of MTD Theory: MTD Systems Theory [206], a Cyber Attack Theory [205], and their interaction [204].
Some definitions from R. Zuang et al. [205, 206], in order to define the concept of an MTD systema:
• A configuration parameter is a unit of configuration infor-mation that can take on a value based on its type.
• A configuration parameter type, is a label identifiable with the domain of possible values that the configuration parameter can assume.
• A configuration state, is a unique assignment of value(s) from the domain of the configuration parameter type to a configuration parameter.
• A configurable system, is a system that is in a given config-uration state, but this state can change based on a set of configuration actions. However, not all configuration states might be valid, because the system has functional goals and policies to comply to. Finally, an MTD system is a configurable system that can adapt its configuration during execution, and it is always in a valid configuration state that can achieve the overall goals of the system. a We prioritize narrative definitions, and point the reader to R. Zuang et al. [205, 206] for the formal definitions. The MTD Evaluaton field deals with methods to evaluate and quantify the effectiveness of MTD systems. This field of research includes mostly the definition of metrics that allow not only the assessment of the effectiveness of a particular MTD system’s technique but also allow the comparison among different ones. The field has practical importance, because metrics can be used to guide the design and implementation of novel MTD systems, or modify existing ones to increase their efficiency against specific attack types.
mtd techniques and taxonomies Finally, the MTD Strategy field covers concrete MTD techniques that can be implemented in sys-tems. We use the terms strategy and technique interchangeably through-out this work, but prioritize the latter. There are more than 100 distinct MTD techniques, and several survey publications [28, 33, 100, 128, 160, 190, 203]. In this subsection, we focus on general design principles shared by them, and in a widely used taxonomy of techniques based on the MP element.
Connectivity and Interoperability: Standards
In the IoT, heterogeneous devices and networks are the norm. Two properties fundamental to make distributed and heterogeneous sys-tems to work together are connectivity and interoperability. Open net-work standards allow devices from different hardware manufacturers or software developers to achieve those properties. In a nutshell, con-nectivity is provided by the IPv6 protocol [40], and interoperability is provided by application-layer protocols like the CoAP [163]. The IETF is a standardization body responsible for most of the network open standards that enable the Internet and the IoT. In Fig. 2.3, we show side by side the IETF’s standard Internet and the IoT network protocol stacks.
Ietf network security for the iot
In this section, we review the most prominent IoT-friendly security proposals designed and published in the context of the IETF. These include protocols, data formats, and frameworks. We use a bottom-up layered approach. Some of these proposals serve as building blocks for more complex security protocols.
Table of contents :
Introduction
1 introduction
1.1 Context and Motivation
1.2 Research Goal and Questions
1.3 Contributions
1.4 Outline i exploration
2 background
2.1 Introduction
2.2 The Moving Target Defense Paradigm
2.2.1 Rationale and Resilience
2.2.2 A Brief History of MTD
2.2.3 Fundamentals, Techniques, and Taxonomies
2.3 The Constrained Internet of Things
2.3.1 Definitions and Context
2.3.2 Connectivity and Interoperability: Standards
2.4 IETF Network Security for the IoT
2.4.1 Network-layer
2.4.2 Transport-layer
2.4.3 Application-layer
2.4.4 A distributed-security toolkit
2.5 Conclusion
3 state of the art of mtd techniques for iot
3.1 Introduction
3.2 Motivations
3.3 Related Work
3.4 Metrics: Definition
3.4.1 Shannon Entropy of the Moving Parameter
3.4.2 Qualitative Entropy-related Metrics
3.5 Methodology
3.5.1 SLR Research Questions
3.5.2 Search Process
3.5.3 Selection Process
3.5.4 Data Extraction Process
3.5.5 Data Synthesis Process
3.6 SLR Results
3.6.1 SLR-RQ-1: How many proposals of MTD techniques for IoT exist? (Status of Field of Study: Quantitative)
3.6.2 SLR-RQ-2: What characteristics can be observed in the proposals? (Status of Field of Study: Qualitative)
3.6.3 SLR-RQ-3: How sound are the security foundations of the proposals?
3.6.4 SLR-RQ-4: To what extent the proposals can be used in a real deployment?
3.6.5 SLR Results detailed per technique
3.7 Limitations of this SLR study
3.8 SLR Summary and Discussion
3.9 Conclusion
4 designing mtd techniques for a resilient iot
4.1 Introduction
4.2 What to Move? Exploring the Network Domain
4.2.1 Physical Layer
4.2.2 Data Link Layer
4.2.3 Network Layer
4.2.4 Transport Layer
4.2.5 Application Layer
4.2.6 Network-layers Summary
4.3 How to Move? IANVS, an MTD Framework for the IoT
4.3.1 Presentation and Rationale
4.3.2 IANVS Schema
4.3.3 Components Details
4.3.4 Security considerations
4.4 When to Move? Synchronized Movement in Distributed Systems
4.5 Conclusion
5 a secure time synchronization protocol for iot
5.1 Introduction
5.2 State of The Art of Secure Time Synchronization
5.3 The LATe Synchronization Protocol
5.3.1 Background
5.3.2 Protocol Entities and Hypothesis
5.3.3 Protocol Goals
5.3.4 Definition
5.3.5 Time Calculation
5.4 LATe’s Formal-method verification using Scyther .
5.4.1 State of the Art of Security Protocols Verification
5.4.2 The Scyther tool and a formal proof of LATe
5.4.3 Results
5.5 Attacks, mitigations and real-world issues
5.5.1 Replay-attack, Injectivity and the Freshness claim
5.5.2 Real nonces and pre-play attack
5.5.3 Reflection Attack
5.5.4 Symmetric Cryptography: Server Key-Management Issues
5.5.5 Protocol refinement
5.6 Comparison of Time Synchronization Protocols
5.7 Conclusion
6 two ianvs-based network mtd techniques
6.1 Introduction
6.2 Design
6.2.1 Definition of Common Components
6.2.2 Technique I: Single Port-Hopping
6.2.3 Technique II: CoAP /.well-known/core URI
6.2.4 Proposals Summary
6.3 Implementation and Evaluation
6.3.1 System: IoT Hardware Platform
6.3.2 Attacker Model
6.3.3 Experimental Setup
6.3.4 Experiment: UDP Port-Hopping Effectiveness against Reconnaissance-Phase of Attack
6.4 Conclusion
7 a phy-layer mtd: physical-layer resilience to insider attacks in iot networks
7.1 Introduction
7.2 Motivation
7.3 Background
7.3.1 Cross-Correlation of Sequences
7.3.2 Pseudo-Random Sequence Sets for WCSs .
7.3.3 CSPRNGs and Stream Ciphers
7.4 Proposal
7.4.1 Overview-Rationale
7.4.2 IANVS-based MTD: CSPR Sequences for DSSS
7.4.3 Implications of PHY Randomization
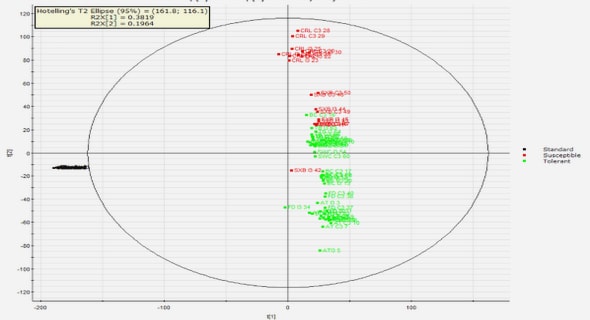
7.5 Cross-Correlation of CSPR Sequence Sets
7.5.1 Motivation
7.5.2 Sequence Sets Generation
7.5.3 Normalized Cross-Correlation Calculation
7.5.4 Statistical Results and Probability Analysis
7.5.5 Analytical CC Distribution of CSPR Sequences
7.5.6 Comparison with NCC of other PR families
7.6 Evaluation: AJ Resilience of Proposal
7.6.1 System Model
7.6.2 Attacker Model
7.6.3 Baseline Evaluation: Broadband Noise Jammer
7.6.4 Upper-Bound Evaluation: Insider Smart Jammer
7.6.5 Evaluation Summary
7.7 Related Work
7.7.1 Correlation of Pseudo-Random Sequences
7.7.2 CSPR-based AJ WCSs
7.8 Discussion
7.8.1 Security-related issues of PR Sequence Sets
7.8.2 Non-security impacts of CSPR Sequence Sets
7.8.3 Relevance of This Proposal for IoT Systems
7.8.4 Key deployment challenges
7.9 Conclusion
Conclusion
8 conclusion and perspectives
8.1 Conclusion
8.2 Future Work
8.2.1 Security: Fundamentals, Design, Proofs, and Openness.
8.2.2 MTD Techniques (What?): Unexplored MPs, SDR, and SDN
8.2.3 MTD Techniques (How?): IANVS-II, Multiple MPs in same domain, adaptive and cross-layer MTDs
8.2.4 Evaluation: The need for usable MTD metrics, security and system-performance/cost (trade-offs).
8.2.5 DSSS physical modulation with CSPR sequences.
Appendix
a résumé en français
b late synchronization protocol: syntax
b.1 LATe Message Encodings
b.1.1 Message 1 – TIC Information
b.1.2 Message 2 – TOC Response
c a phy-layer mtd: unbreakable ss and asymptotic aj evaluation
c.1 Unbreakable Spreading Sequences
c.2 Asymptotic AJ Evaluation
bibliography