Get Complete Project Material File(s) Now! »
CHAPTER 3: RESEARCH DESIGN AND METHODOLOGY
INTRODUCTION
Cybercrime makes the e-commerce space a risky environment for transacting purposes, which ultimately make consumers fearful and reluctant to buy goods and services online. The existing e-commerce assurance measures, such as web seals, have been applied to create trustworthiness assurance, but they have shortcomings that need to be addressed.
This chapter proposes an e-commerce assurance model, PRAHP, for trustworthiness in e-commerce environments. As explained in chapter 1, section 1.3, the objective of this research is to develop an intelligent e-commerce assurance framework, PRAHP, that will promote trustworthiness in e-commerce environments. The primary objective is supported by the following sub-objectives (from section 1.3):
To develop a reliable method of identifying e-commerce assurance model attributes as important compliance measures for e-commerce sites.
To demonstrate the effectiveness of the intelligent framework in addressing security incidents in general e-commerce and on cloud-based platforms.
To determine if the control of weaknesses of the existing assurance models and third-party seals improves the level of security through the use of the framework, specifically in the B2B and B2C e-commerce sites.
To design a way to generate a comprehensive roadmap for e-commerce assurance research types for future research by academics and practitioners.
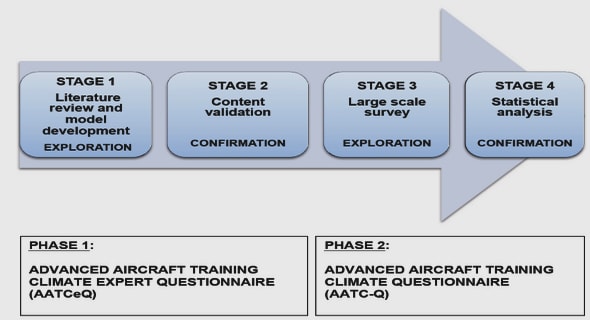
The aim of this section is to discuss the method that was used to achieve the desired research objectives as illuminated through the research questions as well. For the purposes of this research, various methods were used to achieve specific research objectives. Triangulation [95], which is a combination of qualitative and quantitative methods, was used.
During website selection for experimental purposes, an analytical tool determining the size of a website was used. The selection of a sample of the websites was a qualitative process. Quantitative techniques that were adopted included PR and the AHP, although the analysis included some qualitative methods.
DATA COLLECTION
This research study was conducted to cater for various e-commerce market types. In an effort to achieve the desired research objectives, specific data collection methods were used; these are discussed in sections 3.2.1-3.24.
Website analysis
Various e-commerce website types were reviewed manually and also through analytical tools
The size of the website for some of the experiments was vital, considering the expected conclusion that had to be drawn for such experiments. The size of websites was determined based on the inbound, outbound and self-links.
Website analysis was an ideal form of collecting data, since the nature of the study was to collect real-life data, such as the number of website links and the type of service offering by the e-commerce store. The challenge with website analysis is that the information on production websites changes all the time, hence the results may differ over time, i.e. the number of website links. Website analysis was used in this study because of its reliability and accuracy as a data collection method.
Literature survey
The literature survey was conducted as part of this study in order to collect specific data to draw the correct conclusions. In order to identify the weaknesses of the existing e-commerce assurance models, a survey was conducted on a sample of the existing literature to determine the weaknesses of assurance models and ultimately to come up with a roadmap of e-commerce assurance issues. The survey was useful to come up with a reliable method of identifying e-commerce assurance model attributes. The literature used was mainly from accredited journals and thus provided a reliable basis. The shortcoming of collecting data through this method is that it can be very tedious, considering the number of journal articles that had to be reviewed. In instances where not much has been written about a specific e-commerce subject, it can pose a challenge owing to insufficient support of the results and the conclusion.
Statistical analysis
In order to demonstrate the effectiveness of the intelligent framework in addressing security incidents in general e-commerce and on cloud-based platforms, the AHP and PR techniques were used as mathematical tools. A decision table was used to aid in reaching a consensus decision. The use of statistical analysis tools provided efficient and accurate results. A possible challenge of statistical analysis is that some results are technical and they need more detailed explanations for the broader audience to understand.
Customer reviews
Website customer reviews were used to collect data for input into the PRAHP model in order to support objectives 1, 2 and 3, as outlined in section 3.1. These reviews were used as validation mechanism for the website rating. In instances where PRAHP would show a website to be risky to transact from, a negative customer review would be an undisputed statement providing validation of the negative rating. Even though the reviews are reliable, it can be a challenge if, for instance, a website does not have the latest reviews.
PROBLEM FORMULATIONS
This section details how the research problem was formulated mathematically using the AHP and PR techniques.
Modelling analytical hierarchy process
The AHP technique as introduced in section 2.7.2 is one of the techniques employed to evaluate the assurance attributes used in this study. The assurance attributes that have been selected for the purposes of this study are: adaptive legislation (AL), adaptive ISO standards (AI), availability (A), advanced security login (AS) and policy (P).
The AHP technique is used to evaluate and obtain knowledge regarding every attribute in order to reach a decision based on multiple criteria. The technique achieves this objective by providing structure to the assurance model attributes in the form of a hierarchy, where the lower level of the hierarchy is limited by the upper level.
The attributes are assessed ultimately to determine the website’s state of trustworthiness in transacting platforms.
The steps involved in AHP are as follows:
1) Developing a judgement matrix
The AHP technique uses a rating scale of 1 to 9, which consists of the following variables: extremely unimportant, very strongly unimportant, strongly unimportant, moderately unimportant, of equal importance, moderately important, strongly more important, very strongly more important and extremely more important. This constitutes the judging matrix. The rating scale helps to determine the final website rating status for trustworthiness, i.e. red, amber and green (RAG). The judgement scenarios are developed through pairwise comparison.
where Z = comparison matrix. Equation 1 is used for the concurrent activation to complement the AHP and PR techniques.
In order to weigh the elements of the comparison matrix, the priority vector is used.
In order to determine the strength of the consistency ratio and to be able to check whether to evaluate the output or not, the eigenvalue is used.
Where RI = Random index
CR = Consistency ratio
n is the number of compared elements
is eigenvalue.
The eigenvalue is used to assess the strength of the consistency ratio (CR) of the comparative matrix to determine the need for output assessment. The outcome is deemed to have reached a satisfactory level only when CR < 10% or CI < 0.1. In the event of inconsistencies in a matrix, the elements must be adjusted until consistency is reached.
Modelling Page ranking
PR is another component that forms part of the PRAHP model. It is a mathematical model, which is commonly used to rank websites based on the level of importance. As introduced in section 2.7.1, it is used to assess e-commerce assurance and provides an e-commerce assurance rating (EAR).
The EAR model is shown in equation (3).
Based on the equation, for websites linking to A, c(t1)…(tn) are the number of outgoing links where d is a damping factor, which is normally set to 0.85. A low damping factor makes the calculations a lot easier and the convergence happens much more quickly.
Considering the fact that PR allocates a high rank to a node when it has many connections of other highly ranked nodes, it is useful in promoting website trustworthiness on e-commerce sites.
Decision table as fusion
The decision table is used on PRAHP to have clear rules to rank websites based on trustworthiness levels. The decision table works as explained in section 2.7.3 and it aims to assist in reaching a consensus decision through the fusion of two sets of complementary results, as illustrated in the upper section of Figure 15. This is further illustrated by the consensus results as shown in Table 28 of the RAG status indications.
OBJECTIVE FUNCTIONS AND NOTATIONS
The main objective of this research was to develop a connective intelligent e-commerce assurance model, which uses complementary techniques to provide assurance for B2B and B2C e-commerce websites and cloud-based e-commerce environments. The objective of this research is summarised in Figure 14. The techniques involved in the assessment of the attributes are PR and the AHP. The results of the joint assessment by both techniques provide information on the trustworthiness of a website; for instance a website that is found to be untrustworthy is flagged “red” and one that is partially untrustworthy is flagged “amber”, as depicted in Figure 14. A website that is trustworthy will be flagged green.
DEVELOPMENT OF THE PROPOSED PRAHP INTELLIGENT E-COMMERCE ASSURANCE MODEL
Establishing a framework of intelligent e-commerce assurance
The model has been divided into three segments: bottom up, analytical hierarchy assessment, which is complemented by evidential reasoning of PR, which is in turn supplemented by the guidance of the decision table to come to a consensus decision. The model is suitable for use by various e-commerce market types, i.e. B2B, B2C, cloud-based e-commerce environments etc.
In a nutshell, the construction of the PRAHP model is depicted in Figure 15, where the working of the AHP and PR is fused together to reach consensus on the trustworthiness of an e-commerce website.
The selection of attributes was guided by the ISO 27001/27002 standards backed by literature review and statistical assessment [97][98]. The ISO 27001 is a best practice standard for a well-governed and established information security management system. It covers various domains, which must be included in an effective information security management system (ISMS). It also provides a list of controls in annexure A of the standard that must be considered when implementing effective ISMS in electronic environments.
Some of the controls identified in the ISO 27001 standard [98], which relate to the online environment, were used as attributes for this study: availability of information processing, compliance with legal regulation, secure logon, policy and compliance to standards. These were the controls where the attributes of PRAHP were culled for the purposes of this study as availability (A), adaptive legislation (AL), advanced security logon (AS) and adaptive ISO standards (AI).
The attributes of the model will be explained in greater detail in subsequent sections.
Adaptive legislation (AL) as an assurance measure
The nature of the e-commerce environment is much more complex compared to the brick and mortar environment. This is promulgated by many factors, such as the virtual nature of e-commerce platforms, where the transacting parties do not necessarily have any face-to-face interaction.
In the event of cybercrime, where for instance a customer’s personal information can be leaked owing to an information security compromise in a cloud-based e-commerce environment, it would be difficult to establish which laws are applicable in such an event.
In South Africa the Electronic Communications and Transaction (ECT) Act [99] is used to regulate internet and e-commerce related matters to a certain extent, as it outlines the requirements for online vendors.
Different electronic retailers (e-tailers) are governed by various laws based on the country from which they physically operate. The issue of legal jurisdiction in the event of an e-commerce breach can be problematic if the parties affected reside in different countries and the perpetrators reside elsewhere. However, legislation remains important with regard to the trustworthiness of a website. Hence, a website such as Bidorbuy [100], which is an example of a B2C, refer to the South African Protection of Personal Information Act, no. 4 of 2013, to give assurance to customers regarding the protection of their personal information.
Based on the importance of legislation in e-commerce transacting, legislation has been identified as a key attribute that must be included in the development of PRAHP. In the uncertain world of e-commerce, users feel unsafe if they do not know which laws will be used in the event of fraud being committed.
TABLE OF CONTENTS
DECLARATION
DEDICATION
ACKNOWLEDGEMENTS
ABSTRACT
TABLE OF CONTENTS
LIST OF FIGURES
LIST OF TABLES
LIST OF ABBREVIATIONS
CHAPTER 1: INTRODUCTION
1.1 BACKGROUND
1.2 PROBLEM STATEMENT
1.3 RESEARCH OBJECTIVES
1.4 RESEARCH QUESTIONS
1.5 RESEARCH DESIGN
1.6 RESEARCH CONTRIBUTIONS
1.7 RESEARCH ETHICAL CONSIDERATIONS
1.8 SCOPE AND CONTEXT OF THE STUDY
1.9 RESEARCH SYNOPSIS
1.10 CHAPTER SUMMARY
CHAPTER 2: LITERATURE SURVEY AND THEORETICAL BACKGROUND
2.1 PRELIMINARIES
2.2 E-COMMERCE ASSURANCE MODELS AND TRUSTWORTHINESS ISSUES
2.3 POPULAR AREAS OF E-COMMERCE ASSURANCE
2.4 BUSINESS-TO-CONSUMER ASSURANCE
2.5 BUSINESS-TO-BUSINESS ASSURANCE
2.6 CLOUD-BASED E-COMMERCE ASSURANCE
2.7 SELECTED MACHINE LEARNING THEORIES
2.8 CHAPTER SUMMARY
CHAPTER 3: RESEARCH DESIGN AND METHODOLOGY
3.1 INTRODUCTION
3.2 DATA COLLECTION
3.3 PROBLEM FORMULATIONS
3.4 OBJECTIVE FUNCTIONS AND NOTATIONS
3.5 DEVELOPMENT OF THE PROPOSED PRAHP INTELLIGENT E-COMMERCE ASSURANCE MODEL
3.6 EVALUATION AND VALIDATION MECHANISM
3.7 PRAHP DEPLOYMENT SCENARIO
3.8 CHAPTER SUMMARY
CHAPTER 4 – EXPERIMENTAL EVALUATIONS AND RESULTS
4.1 OVERALL EXPERIMENTAL SETUP
4.2. EXPERIMENT 1: ANALYSIS OF E-COMMERCE ASSURANCE MODELS AND PRAHP ATTRIBUTES
4.3 EXPERIMENT 2: INVESTIGATING CORRELATION OF PRAHP ASSURANCE ATTRIBUTES
4.4 EXPERIMENT 3: PRAHP ASSURANCE FOR SIZEABLE GENERAL E-COMMERCE ENTERPRISES
4.5 EXPERIMENT 4: PRAHP EVALUATION ON PRIVATE AND PUBLIC CLOUD-BASED ASSURANCE
4.6 EXPERIMENT 5: PRAHP EVALUATION ON B2C AND B2B E-COMMERCE WEBSITES
4.7 CHAPTER SUMMARY
CHAPTER 5: OPEN E-COMMERCE ASSURANCE RESEARCH
5.1 INTRODUCTION
5.2 IMPLEMENTATION
5.3 PATTERN OF ARTICLES BY YEAR OF PUBLICATION
5.4 PATTERN OF ASSURANCE ARTICLES BY JOURNALS
5.5 PATTERN OF E-COMMERCE ASSURANCE ARTICLES BY TOPICS
5.6 OPEN RESEARCH QUESTIONS
5.7. COMPARATIVE EVALUATIONS OF E-COMMERCE ASSURANCE MODELS
CHAPTER 6: CONCLUSION AND FUTURE DIRECTIONS
6.1 OVERVIEW OF THE STUDY/RESEARCH SUMMARY
6.2 RESOLUTIONS TO RESEARCH QUESTIONS
6.3 SUMMARY OF CONTRIBUTIONS
6.4 RECOMMENDATIONS
6.5 LIMITATIONS AND FUTURE DIRECTIONS
GET THE COMPLETE PROJECT
Development of an intelligent e-commerce assurance model to promote trust in online shopping environments