Get Complete Project Material File(s) Now! »
CHAPTER THREE: INTERNATIONAL PERSPECTIVE ON THE POLICING OF COUNTERFEIT
INTRODUCTION
Countries are globalising their relations and businesses are internationalising their operations to grow and be competitive in the global market. In the same vein, criminals are also maximising their ill-gotten profit. Sonmez (2014:758) asserts that counterfeit crime is attractive business to the free riders. In addition, Kerns (2016:573) equates it with the capturing of one’s ideas in developing and imitating products without incurring significant investment thereby eliminating the competitive edge of the original product owner. Counterfeit crime is also regarded as a moving target, which could not be confined to a single country because products that are produced in one country are sold in different countries with different statutes that define what is crime and what is not.
The prevention of crime is the responsibility of the government but when it comes to the prevention of counterfeit goods, many countries seem not to prioritise its policing. Another problematic issue is lack of synergy in criminalising counterfeiting in many countries and this leads to indecisiveness in developing and implementing a focused campaign in eradicating this. This is despite the fact that the United Nations adopted resolution 1373 in 2001 to prevent and suppress the financing of terrorism (United Nations, 2001).
This chapter deals with the policing of counterfeit goods, focusing specifically at the nexus between counterfeit and organised crime, counterfeit and terrorism, modus operandi, factors causing the rise of counterfeit and increase of counterfeiters. In addition, the chapter discusses international framework on policing counterfeit, and various international conventions and treaties.
COUNTERFEIT AND ORGANISED CRIME
The availability of volumes of counterfeit goods reflect an increase in the types of products which are counterfeited and an increase in the number of parties involved in this activity (Ene & Mihaescu, 2014:54). In venturing into a particular criminal enterprise, organised criminals first weigh in on the level of profit attainable from any given illicit activity as well as the level of risk involved (UNICRI, 2009:83). Blackstone and Hakim (2013:158) and Rojek (2016:6) support this when they assert that counterfeit crime has grown exponentially as a crime of choice for organised criminals.
According to Spink, Meyer, Park, and Heinonen (2013:6), the criminals involved in counterfeit could be categorised as follows:
Individuals or Small Groups: Some counterfeit cases involve individuals or small groups who operate out of their homes, garages, or small storage facilities. This category tends not to be the main focus of the police as compared to larger groups who engage in more significant counterfeit activities as well as committing other serious offenses.
General Criminal Enterprises: This is a category of transnational, national or local groupings of highly centralised enterprise that is run by criminals who engage in illegal activities for money and profit purposes. An Asian criminal enterprise where 30 people were charged with smuggling counterfeit goods worth 40 million USA dollars into USA is a classical example of general criminal enterprises. Similar to this group is the operations of the “JAH” an organisation based in West Africa that specialises in the sale of counterfeit and pirated products over the world. This organisation established bases in many countries and engage in money laundering as well (Heinonen & Wilson, 2012:279).
Organised Crime Members: Organised crime members are a specialised subset of a criminal enterprise that maintains its position through the use of violence. An example of this is the Lim organisation in Asia that commits counterfeit and piracy crime, sabotage businesses, extort money from business owners, and threaten law enforcement officials with retaliation and constantly threaten to kidnap their families (Spink et al., 2013:60).
Terrorist Organisations: Organisations that support terrorism use counterfeit and piracy as one of the methods to raise funds. A distinction exists between organisations that support terrorism by merely providing funding and resources versus terrorist organisations who engage in the actual violent terrorist activities (Choo & Smith, 2008:39).
Warez Groups: Their motivation for committing counterfeit and piracy is for personal fame and notoriety. This sophisticated and hierarchical group specialises in distributing counterfeited goods and piracy software via the internet.
Counterfeit crime can be committed in two ways, namely – deceptive and non-deceptive counterfeit. In deceptive counterfeit crime, consumers do not realise that they are buying a counterfeit product. This type of counterfeit crime can be minimised through proactive policing in order to stop the supply of the infringing products to the markets and consumers. Effective prevention and deterrence of this crime could involve the use of intelligence as well as the imposition of harsher sentences on convicted counterfeiters. However, UNODC (2016:190) indicates the difficulty of locating the culprits owing to the difficulty of locating the area where goods are counterfeited as this can be produced anywhere in the world where the labour is cheap and laws are weak.
Conversely, non-deceptive counterfeit relates to the counterfeit that is bought by consumers wilfully knowing it to be counterfeit (Zibas, 2012:23-25). In this case as well, proactive policing may to a certain extent still be employed to minimise this crime because consumers are technically accomplices to the crime. Large (2009:3) argues that counterfeiting could be committed in an organised manner by members with full knowledge of the organisation. This needs high level of sophistication as organised crime needs significant financial resources to meet periodic financial needs, cover any incidental expenses and to support the vertical or horizontal expansion of their enterprise (Levi, Shentov & Todorov, 2015:342). Once a smuggling operation is developed, it can generate sufficient profit to allow further investments in the scheme in a number of self-financing cycles (Levi, et al., 2015:345).
Police corruption is one of the factors that stifle the fight against counterfeit crime and makes it very difficult to successfully deal with this crime. Moreover, Park (2008:54) emphasises this by stating that when state officials are involved in organised crime, it becomes difficult to deal with it. What compound this is the fact that police organisations are unable to hire highly trained cybercrime investigators, lawyers, auditors, accountants and engineers that possess the knowledge to deal with such sophisticated aspects of organised crime owing to budgetary constraints (Blackstone & Hakim, 2013:161). As a result, this allows criminals who have sophisticated measures that cannot be successfully dealt with by ordinary police officers to have an upper hand when producing counterfeit goods. They use sophisticated skills and expertise to perfect counterfeit goods to look like genuine products (Von Lampe, 2011:158).
COUNTERFEIT AND TERRORISM
After the confirmation of the involvement of the organised crime in counterfeiting activities in 2010, the United Nations Commission on Crime Prevention and Criminal Justice took a decision to strengthen crime prevention and criminal justice responses in the policing of counterfeit crime, piracy and terrorism. Counterfeit crime focuses on economic profit and the acquisition of wealth through the illegal market while terrorism is motivated by ideological aims and desire for political change as well as focusing on acquiring resources (Sullivan, Chermak, Wilson & Freilich, 2014:359). The nexus between these crimes is that counterfeit is used to generate the money that fund terrorist activities. A small group may focus on counterfeiting whereas other groups may focus on many other activities of terrorism (Spink et al., 2013:7).
The link between counterfeit crime and terrorism has been demonstrated in cases of organisations such as Hezbollah, Hamas, Harakat al-Shabaab al-Mujahideen, Al-Qaeda, Revolutionary Armed Forces of Colombia, and Islamic Jihad. These organisations are known to be trading in counterfeit and conducting illicit businesses such as dealing in piracy to finance their terrorism activities (Choo & Smith, 2008:39). They are classified as terrorist organisations by the USA State Department on the list of Foreign Terrorist Organisation (US Department of State, 2017). As explained previously, counterfeit crime proceeds are mostly used by criminals to fund other crimes such as terrorism around the world. Meaney (2004:99-100) categorises counterfeit criminals into two groups, namely – marauders criminals, which are criminals who operate close to their residential area and commuters criminals, which are those criminals who commit their criminal acts far away from their residential places.
The 21st century has seen a globalised enormity of the counterfeit industry and market as well as the ease by which consumer ideas and goods can be transported around the world by technologies. This is expedited by the availability of digital and networked technologies that make information on products easily accessible. The International Trademark Association (INTA) states that with the distribution of counterfeit products online, sellers are more accessible to their market, anonymity of the seller is confined and it is easy for the counterfeiter to deceive their customer into believing that the goods are genuine, as merchandise is often received after payment (International Trademark Association, 2009:1). Figure 7 shows EU picture of the categories of goods whose intellectual property is often infringed.
Figure 7 above illustrates that, in 2007, the majority of articles seized by customs were infringing on a trademark and covered a wide variety across all product sectors. With regard to patent infringements, the main products involved concerned electronic equipment. With regard to copyright infringements, CDs and DVDs were the products most affected, as well as a wide variety of products containing protected images such as well-known comic figures. In design rights, most infringements concerned toys and accessories for cell phones.
Counterfeit is a lucrative business for syndicates and international criminal organisations because they are able to decipher and reverse some engineered security measures placed in some of the goods. Although this requires more time, skills and money, the sophistication and financial muscle of syndicates and organised criminal organisations make it possible (Choo & Smith, 2008:43).
MODUS OPERANDI IN COUNTERFEITING
Modus operandi is useful for the prevention and resolution of crime by the police as it enables them to analyse the trademarks of the perpetrators in order to identify those who committed crime (Berg & Shearing, 2011:25). Without the use of the modus operandi, it could not be possible for the police to build the database that makes it easy to match it with the method used in the perpetration of a particular crime. More so, owing to the clandestine nature of counterfeiting, it is difficult to get to how it is carried out and its extent owing to lack of precise figures (Jolly & Philpott, 2004:214; United Nations Office on Drugs and Crime, 2014c:173). This tends to be compounded by the increase of counterfeit crime in informal markets where there are loosely controlled supply chain systems that lack proper monitoring and effective policing in many countries (OECD, 2008:82).
The booming international trade and the concomitant signing of trade agreements have resulted in the weakening of the security in national borders, therefore enabling illicit goods to flood countries. As a result, it is easy for syndicates and organised criminal organisations to create alliances involving different criminal organisations both nationally and internationally. The Sicilian Mafia also known as Cosa Nostra that was established in the 19th century in Sicily, Italy is the classical example of a network of organised crime groups based in Italy and America. The group bonded together in several groups to protect themselves and carry out their extra-judicial activities of torturing people. They also practiced as small armies and extorted money from business people. During the 21st century, they became adept at corrupting government officials and intimidating politicians to vote for their preferred candidates at political congresses (Balsamo, 2006:373-377). They initiated a series of alliances with criminal organisations from other countries to create a division of labour and to subdivide the counterfeit market. By so doing, counterfeit crime is attaining greater operational efficiency and maximising profits with links between different criminal activities in terms of both their financing and the money laundering of their proceeds. Commercial specialisation has been repudiated in favour of the simultaneous trade and supply of different categories of illegal goods and counterfeiting that has become a fundamental element of this scheme (Choo & Smith, 2008:50).
CHAPTER ONE: GENERAL ORIENTATION
1.1 INTRODUCTION
1.2 THE BACKGROUND OF THE STUDY
1.3 PROBLEM STATEMENT
1.4 THE RESEARCH QUESTION
1.5 RESEARCH OBJECTIVES
1.6 THE SIGNIFICANCE OF THE STUDY
1.7 DEMARCATION OF THE STUDY
1.8 DEFINITION OF KEY THEORETICAL CONCEPTS
1.9 OUTLINE OF THE STUDY
1.10 CONCLUSIONS
CHAPTER TWO: HISTORICAL BACKGROUND AND THEORETICAL EXPLANATION OF COUNTERFEIT CRIME
2.1 INTRODUCTION
2.2 HISTORICAL BACKGROUND OF COUNTERFEIT
2.3 IMPACT OF COUNTERFEIT
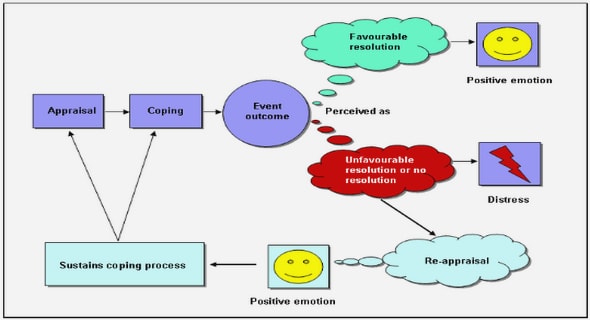
2.4 THEORETICAL EXPLANATION OF COUNTERFEIT
2.5 CONCLUSION
CHAPTER THREE: INTERNATIONAL PERSPECTIVE ON THE POLICING OF COUNTERFEIT
3.1 INTRODUCTION
3.2 COUNTERFEIT AND ORGANISED CRIME
3.3 COUNTERFEIT AND TERRORISM
3.4 MODUS OPERANDI IN COUNTERFEITING
3.5 FACTORS CAUSING THE RISE OF COUNTERFEIT AND INCREASE OF COUNTERFEITERS
3.6 INTERNATIONAL LEGAL FRAMEWORK ON POLICING COUNTERFEIT
3.7 INTERNATIONAL CRIMINAL POLICE ORGANISATION
3.8 AGREEMENT ON TRADE RELATED ASPECTS OF INTELLECTUAL PROPERTY RIGHTS
3.9 POLICING OF COUNTERFEIT: AN INTERNATIONAL PERSPECTIVE
3.10 POLICING OF COUNTERFEIT CRIME IN SELECTED COUNTRIES
3.11 CONCLUSION
CHAPTER FOUR: THE POLICING OF COUNTERFEIT IN SOUTH AFRICA
4.1 INTRODUCTION
4.2 THE PROBLEM OF COUNTERFEIT IN SOUTH AFRICA
4.3 RATIONALE FOR POLICING COUNTERFEIT IN SOUTH AFRICA
4.4 THE USE OF DETECTION TOOLS AND PROACTIVE POLICING IN THE POLICING OF COUNTERFEIT
4.5 SOUTH AFRICAN LEGAL FRAMEWORK ON POLICING COUNTERFEIT
4.6 FACTORS ENCOURAGING COUNTERFEIT
4.7 CONCLUSION
CHAPTER FIVE: ADJUDICATION OF COUNTERFEIT IN SOUTH AFRICA
5.1 INTRODUCTION
5.2 THE ROLE OF CRIMINAL JUSTICE SYSTEM IN COUNTERFEIT POLICING
5.3 THEORIES OF PUNISHMENT
5.4 COUNTERFEIT INVESTIGATION PROCESS
5.5 ADJUDICATION OF COUNTERFEIT
5.6 THE PROSECUTION OF COUNTERFEIT
5.7 SANCTION
5.8 CONCLUSION
CHAPTER SIX: RESEARCH METHODOLOGY
6.1 INTRODUCTION
6.2 RESEARCH DESIGN
6.3 RESEARCH APPROACH
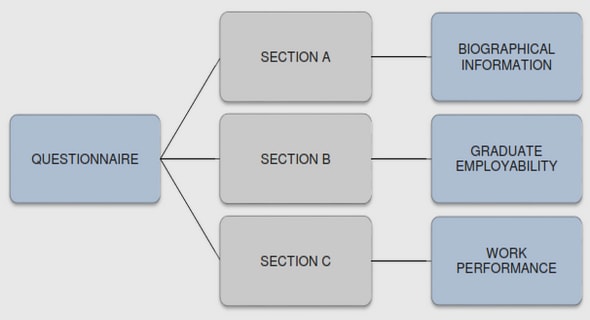
6.4 RESEARCH METHODOLOGY
6.5 PILOT STUDY
6.6 POPULATION AND SAMPLING
6.7 DATA COLLECTION METHODS
6.8 DATA ANALYSIS
6.9 DATA INTEGRITY (RELIABILITY AND VALIDITY ISSUES)
6.10 ETHICAL CONSIDERATIONS
6.11 CHALLENGES ENCOUNTERED IN THE STUDY
6.12 CONCLUSION
CHAPTER SEVEN: PRESENTATION OF THE RESEARCH FINDINGS
7.1 INTRODUCTION
7.2 FINDINGS
7.3 SPECIFIC FINDINGS
7.4 GENERAL FINDINGS
7.5 CONCLUSION
CHAPTER EIGHT: RECOMMENDATIONS AND CONCLUSION
8.1 INTRODUCTION
8.2 RECOMMENDATIONS
8.3 CONCLUSION
REFERENCES
GET THE COMPLETE PROJECT
A CRITICAL ANALYSIS OF THE POLICING OF COUNTERFEIT GOODS IN SOUTH AFRICA