Get Complete Project Material File(s) Now! »
Properties of biometric modalities
Biometric authentication presents several advantages compared to traditional iden-tification ways like passwords or cards because it establishes a strong link between an individual and their identity. Principal properties of a biometric modality are the following:
• Universality: The whole population should possess this modality (physical or behavioral characteristic).
• Distinctiveness: Two different individuals must have different biometric representations.
• Stability: To ensure individual authentication success, biometric modality should be relatively stable over time and it also has to be stable regardless conditions of acquisition (external conditions, emotional conditions of the person, etc.).
• Collectability: The biometric modality must be acquired.
• Acceptance: The acceptance and the facility of usage are related to the acquisition constraints of a biometric modality.
• Circumvention: The biometric modality must not be easily falsified.
• Performance: Biometric recognition should be accurate, fast and robust with regards to operational and environmental changes.
All modalities do not possess all these properties, or may possess them with dif-ferent degrees. Hence, there is no ideal or perfect modality. The trade-off between presence and absence of some of these properties is required according to each system needs, regarding the choice of biometric modality.
Advantages and disadvantages of each biometric modality
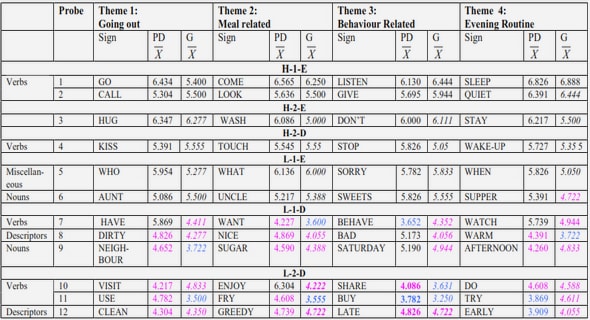
A comparison between different biometric modalities according to the seven prop-erties mentioned previously (universality, distinctiveness, stability, collectability, acceptance, Circumvention, performance) is presented in table 2.1. The quality degree accorded to each modality is classified into three classes: high, medium and low referred to the following notations • • •, • • and •, respectively.
This table originating from [Jain 2004] indicates that behavioral biometric modal-ities (keystroke, odor or signature) present low recognition performances unlike intrusive data such as methods based on DNA or retina. However, data given from palmprint or hand geometry present the advantage that they do not pos-sess any low criterion compared to other modalities. Moreover, they are acquired from a single biometric modality which is hand trait. These advantages justify the choice of these modalities which are treated in this thesis.
Verification and identification
There are several kinds of applications which require users authentication. These applications may be classified into two categories namely identity verification and identification.
• Identity verification corresponds to verifying the claimed identity by compar-ing the acquired biometric data with its corresponding biometric templates stored in system database. In such system, a person who wants to be rec-ognized claims an identity using a persons identification number or a smart card and the system conducts a one-to-one comparison to finally determine if the claim is true or false (by answering to this question: ”Does this bio-metric data correspond really to Mr. Bob?”). Identity verification is an important task which aims to avoid the use of the same identity by various people [Wayman 2001].
Limitations of unimodal biometric systems
Biometry establishes a physical link between an individual and their identity and permits, hence, a more reliable identification than traditional ways like cards or keys. However, biometric systems have some limitations which prevent their use for all current applications. The main limitation incorporates performance. De-spite possible security risks of traditional identification ways (loss, robbery or falsification), they are 100% efficient in terms of recognition. If the password is correct, the response of system is ”Right”, otherwise, the response is ”False”, so the matching is 100% accurate.
However, biometric systems have not succeed so far to achieve this accurate recog-nition because they are based on a similarity score which is a real number de-scribing the similarity degree between two biometric data. Therefore, the decision module is important for biometric system since a decision threshold has to be determined and applied to similarity score. If the score is higher than threshold value, the two samples are from the same individual and identity is well verified, otherwise, the two samples are from different individuals and the person is rejected (identity not verified). These variations in biometric data and the absence of an accurate matching are due to several factors:
• Noise effect in sensed data due to the imperfect conditions of data acqui-sition. Indeed, the captured biometric data could be noisy or distorted. In biometric information, variations (such as bad illumination or noisy acquisi-tion) might generate inaccurate matching in database i.e. an imposter might be incorrectly accepted or an enrolled person could be incorrectly rejected.
• Non universality: although biometric traits are expected to exist among each single individual of a given population, there are some exceptions, in which an individual is not able to present their biometric trait because of pathological conditions, or working environments characterized by manual activities which may even erase fingerprint or palmprint data.
• Temporal variability and non uniqueness are also called intra-class variability (modality variation for an individual) and inter-class variability (variation between modalities of many individuals) may reduce the identifi-cation accuracy of biometric systems. For example, in the case of identical twins, the principal lines features of their palms may lead to inaccurate matching due to incorrect data inducing a false rejection.
• Spoof attacks: biometric systems are vulnerable to spoof attacks where the biometric trait may be imitated or forged. For instance, rubber fingerprints can be used for spoofing. In addition, less discriminative biometric traits are also prone to such attacks.
Different multi-types
Multimodal biometric systems reduce limitations of unimodal biometric systems by combining several systems. Five types of multimodal biometric system (figure
2.6) can be defined as follows:
• Multi-sensors: It consists in combining various sensors to acquire the same modality. For example, both optical sensor and multispectral sensor may be used for fingerprint acquisition.
• Multi-instances: It consists in combining several instances of the same bio-metric. For example, the acquisition of several images of face with different poses, expressions or illumination.
• Multi-representations: It consists in using several representations to treat the same image acquired. For example, the case of hand biometric which may be represented by its shape and its texture features.
• Multi-samples: It consists in combining various samples of the same modal-ity. For example, two fingerprints of different fingers or two irises. In this case, different references have to be acquired in registration phase, unlike multi-instances which require a single reference.
• Multi-biometrics: It consists in fusing multiple biometric modalities such as hand geometry and palmprint. A multimodal system may also combine these different types, for instance the fusion of face and prints of different fingers.
Table of contents :
Contents
List of Figures
List of Tables
1 General introduction
1.1 Context of the research and motivation
1.2 Problem statement and objectives
1.3 Contributions
1.4 Outline
I LITERATURE REVIEW
2 General context of biometry
2.1 Introduction
2.2 Identity verification of a biometric system
2.2.1 Identity verification
2.2.2 Biometry
2.2.3 Biometric modalities
2.2.4 Properties of biometric modalities
2.2.5 Advantages and disadvantages of each biometric modality .
2.2.6 Verification and identification
2.2.7 Structure of a biometric system
2.2.8 Evaluation of a biometric system
2.3 Multimodality
2.3.1 Limitations of unimodal biometric systems
2.3.2 Different multi-types
2.3.3 Architectures of multimodal systems
2.3.4 Fusion levels
2.4 Why hand modality ?
2.4.1 Presentation of some biometric modalities of the hand .
2.4.2 Principal challenges of hand modality
2.5 Conclusion
3 Hand shape and palmprint modalities: a survey
3.1 Introduction
3.2 Hand Shape Modality
3.2.1 Hand image acquisition
3.2.2 Hand detection
3.2.3 Hand feature extraction
3.2.4 Matching module
3.2.5 Decision-making module
3.2.6 Discussion and overview of different hand shape approaches
3.3 Palmprint modality
3.3.1 Characteristics of palmprint modality
3.3.2 Palmprint image acquisition
3.3.3 Palmprint Region Of Interest (ROI) extraction
3.3.4 Palmprint feature extraction
3.3.5 Overview of different palmprint approaches
3.4 Multimodal hand shape and palmprint biometrics
3.4.1 Challenges of using multimodality
3.4.2 Design of multimodal biometric systems
3.4.3 Overview and discussion of hand shape and palmprint fusion approaches
3.5 Conclusion
II CONTRIBUTIONS
4 Verification approach based hand shape modality
4.1 Introduction
4.2 Methods and techniques
4.2.1 Scale Invariant Feature Transform (SIFT)
4.2.2 Gabor filters
4.3 The proposed Sift Matching Refinement based Hand Shape Verification (SMRHSV)
4.3.1 Preprocessing module
4.3.2 The matching refinement
4.4 Experimental evaluation
4.4.1 Experimental corpus
4.4.2 Verification results
4.4.3 Execution time performance
4.5 Discussion and comparison
4.6 Conclusion
5 Identification approach based palmprint modality
5.1 Introduction
5.2 Methods and techniques
5.2.1 Sparse representation (SR) concept
5.2.2 Support Vector Machines (SVM)
5.3 Proposed identification approach based palmprint modality .
5.3.1 Palmprint ROI extraction
5.3.2 Feature extraction
5.3.3 Palmprint identification
5.4 Experimental evaluation
5.4.1 Proposed prototype
5.4.2 Experimental results
5.4.3 Execution time performance
5.5 Conclusion
6 Proposed hand multi-types fusion for multimodality
6.1 Introduction
6.2 Multi-representation hand shape verification method
6.2.1 Feature extraction module
6.2.2 Matching score
6.2.3 Information fusion method
6.2.4 Experiments and results
6.3 Multi-biometric hand recognition method
6.3.1 Hand shape and palmprint fusion for persons verification .
6.3.2 Hand shape and palmprint fusion for persons identification .
6.4 Multi-instance palmprint identification method
6.4.1 Fusion at rank level using probability distribution
6.4.2 Experimental evaluation
6.5 Summary and conclusion
7 Conclusions and future work
Bibliography